APPLICATION SECURITY
Knowledge Base
Search Our Knowledge Base
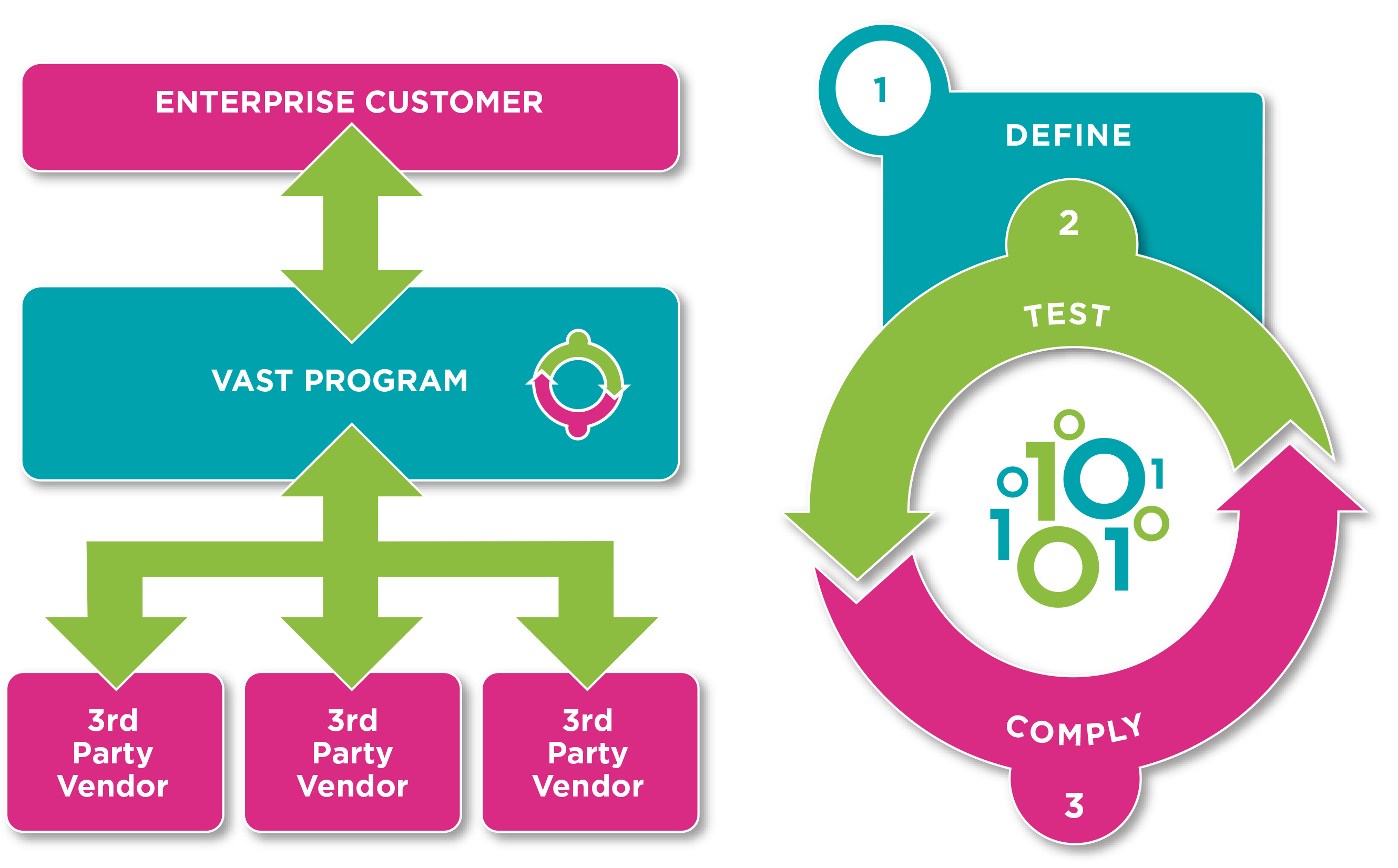
Vendor Application Security Testing
VAST reduces the risk associated with third-party software — so you can innovate with more speed and confidence than ever. With VAST, we manage the entire third-party program for you as a cloud-based service — and work directly with vendors in your software supply chain to ensure they’re compliant with your corporate security policies.
Leading organizations such as OWASP, the PCI Council, FS-ISAC and NIST are raising awareness about the need to better understand and reduce the security risks associated with the use of third-party software.
Why? Because when you install applications or software components from a third-party, you also take ownership of all the vulnerabilities in their software.
And seeing how 65 percent of a typical enterprise portfolio comes from third-parties, there’s a lot of risk to take on—especially when 82 percent of applications fail to comply with enterprise security standards on their first pass.**
VAST ensures that all externally developed software—whether it’s commercial off-the-shelf, SaaS, third-party libraries, outsourced or open source—complies with your security policies. We’ll manage every aspect of the process, including contacting vendors and working closely with them to rapidly identify and remediate application threats.
To enhance the compliance of third-party suppliers with your corporate security policies, Veracode will:
-
Act as an independent party for enterprises procuring third-party software and for software vendors selling to enterprises.
-
Analyze third-party applications and attest to their security posture while protecting the vendor’s intellectual property through the use of binary static analysis.
-
Provide software vendors with detailed and prioritized remediation guidance.
-
Keep enterprise customers up to date with detailed program status reporting from vendors within the program.
-
Broker and manage the program as well as create attainable compliance goals.
**SOURCE: Veracode State of Security Report