Encapsulation Vulnerabilities
What Is an Encapsulation Vulnerability?
Encapsulation refers to a programming approach that revolves around data and functions contained, or encapsulated, within a set of operating instructions. Applications become vulnerable to an attack when they fail to separate or differentiate critical data or functionality within components. When an encapsulation vulnerability exists, bad code creeps across software components or “leaks” from an application. This problem can also lead to cross-domain attacks. Without strong and clearly defined boundaries between control spheres, attackers can gain unauthorized access to data and functions.
Ask a Qualified AppSec Expert
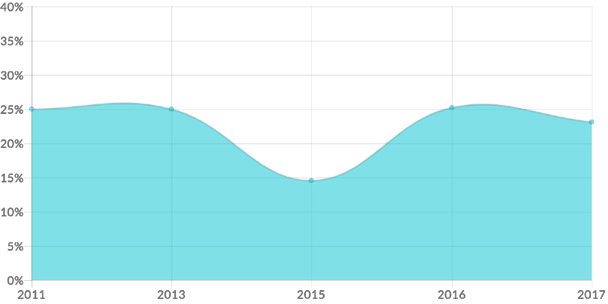
Encapsulation Is a Persistent Threat
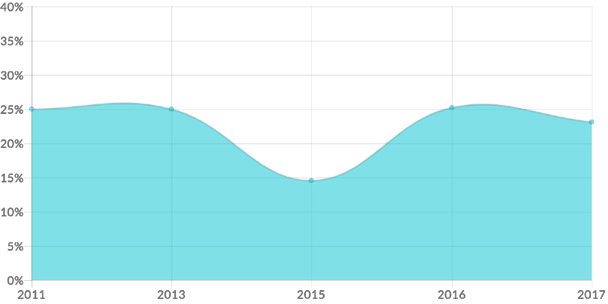
Source: Veracode State of Software Security 2017
Anatomy of an Attack
Step 1: An attacker initiates a non-typical request to a web application or other exposure point and views the resulting error codes. These error codes provide clues about technologies, operating systems, product versions, and other system details.
Step 2: After obtaining detailed system or application information—including things like debugging information or logging data—the attacker fashions an assault based on known vulnerabilities. There are a variety of attack methods possible. These include trust boundary violations, protection mechanism failures, and deserialization of untrusted data.
Step 3: The attacker launches the attack to deny service, cause security mechanisms to fail, or crash a server. This breach can take place via a mobile platform, web server, or other computing system.
The Impact of an Attack
An encapsulation attack can lead to problems that range from relatively benign to catastrophic. By denying service, critical system functionality may be unavailable to users for a period of time. Switching off security controls may lead to extensive damage, including modified, destroyed or stolen data. There’s also the possibility of damage to applications and other tools and resources, or a ransomware attack.
Real-Life Attack Example
In 2016, the San Francisco Metropolitan Transit Agency’s Municipal Rail (known as MUNI) suffered a significant ransomware attack based on an encapsulation vulnerability. The perpetrator demanded a US $73,000 ransom from the transit authority. The transit agency had neglected to patch a Java deserialization flaw that had existed for more than a year. Fortunately, MUNI officials were able to quickly restore systems from backups and thus avoid paying the ransom.
Attack and Defense Code Examples
Example #1:
This example in C Language prints the path environment variable to the standard error stream:
char* path = getenv("PATH");
...
sprintf(stderr, "cannot find exe on path %s\n", path);
Example #2:
This example in Java prints an exception code to the standard error stream:
try {
...
} catch (Exception e) {
e.printStackTrace();
}
(bad code)
try {
...
} catch (Exception e) {
Console.Writeline(e);
}
The above example exposes a system to a breach by allowing an attacker to dump data into a console, write data to a log file, or view it as a remote user. The system may provide specific information about system vulnerabilities. It might also deliver general information or clues about the underlying operating system in use, the types or nature of applications, and the approach developers have taken in coding applications.
Example #3:
Here’s an example in C#
string cs="database=northwind; server=mySQLServer...";
SqlConnection conn=new SqlConnection(cs);
...
Console.Writeline(cs);
This example exploits a system or application using the same type of methodology as the Java example above.
Preventing Damage
The discovery of an encapsulation vulnerability requires an organization to cut access to the affected application, database, or system until it can be fully protected. In the case of ransomware, a backup allows the organization to return to a working state quickly and without paying the fee demanded by the attacker.
Remediation Is Critical
It’s critical to check all code for encapsulation vulnerabilities and protect all application sessions from information leakage. One of the most effective tools for this is static analysis. It’s also vitally important to understand how code functions and retest it in different environments and for different uses. For example, a code string may pose no risk in a single-user environment but may introduce a huge vulnerability in a multi-user framework. In a multithreading environment, it’s important to avoid storing user data in Servlet member fields and member fields to store information in the Servlet.
Veracode Can Aid in the Defense Against Encapsulation Vulnerabilities
Veracode Web Application Scanning can safely, accurately, and quickly discover web application flaws, including SQL injection, in running web applications, in either production or pre-production environments.
Veracode Static Analysis can accurately identify SQL injection vulnerabilities and other flaws in your application and its third-party components and tell your developers exactly where and how to repair them. All without ever looking at the source code.
Our cloud-based application security platform helps you manage your application security program, track progress, and educate your developers on avoiding and repairing SQL injection and other security flaws through integrated eLearning materials.
Secure Coding Handbook
About Veracode Developer Training
Common Web Application Vulnerabilities
Failure to Restrict URL Access
Insecure Cryptographic Storage