Reduce Risk. Secure Your SDLC.
Veracode empowers secure development by identifying and resolving application risks with decades of expertise and AI-driven insights.
Build, Scale and Secure Software Fast
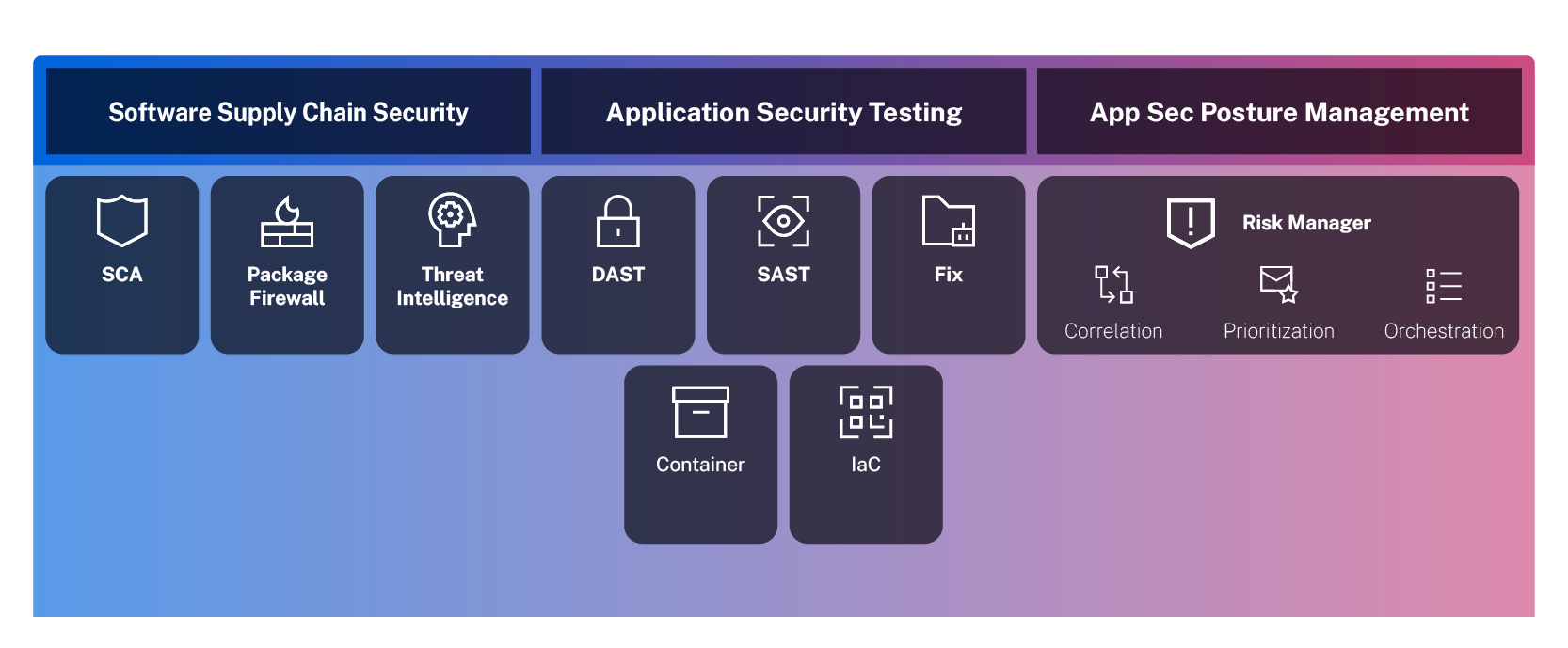
A suite of application risk management tools purposely built to reduce risk, catch vulnerabilities early, and empower developers to deliver secure code across the SDLC.
Essential AppSec Features
Streamlined Tools for Reducing Risk and Secure Coding Success
Empower your SDLC with cutting-edge tools that detect vulnerabilities, streamline remediation, and integrate seamlessly—delivering robust protection and actionable insights across every stage
Code to Cloud Scanning
Drive innovation with SAST, DAST, SCA, IaC, and container scans, seamlessly integrated into IDEs for instant, actionable insights
AI-powered Remediation
Boost productivity through AI-powered remediation, fixing flaws in minutes vs. hours.
Security and SDLC Integrations
Integrate testing into the tools developers use and give critical insights to security teams.
Actionable Visibility
Increase visibility with real-time, actionable insights to prioritize and remediate flaws across complex environments.
Next Best Actions
Reduce risk with automated root-cause analysis to remediate the most urgent security issues first.
On-demand Expertise
Empower secure coding practices across the SDLC by leveraging expert guidance to tackle challenges effectively.
Secure Every Step of Your SDLC
Integrate, Automate, and Secure Your Development Pipeline.