Credentials Management Flaws Information, Tutorial, and Cheat Sheet
- What is a credentials management attack?
- What is the best way to handle passwords in Java, PHP, and other languages?
- How do you prevent credentials management flaws?
- How do you remediate credentials management flaws?
Access to many websites, applications, devices, and networks is controlled by a set of credentials, most commonly a username and password. Credentials management attacks attempt to breach username and password pairs to take control over user accounts, which can leave data vulnerable. A credentials management flaw may open systems, sites, and applications to threat if an attacker can breach this data and gain control of a user account. Depending on the access levels of the breached accounts, attackers making use of a credentials management vulnerability may be able to initiate financial transactions, change or steal data including personally identifiable information (PII), impersonate the authenticated user, install malware, and gain further access to data and systems.
By understanding how to identify, prevent, and remediate credentials management flaws, developers and security professionals can protect their organizations from these types of attacks. Veracode’s suite of solutions can give you the tools to detect vulnerabilities and provide a fix, even before your site or application goes into production.
What Is a Credentials Management Attack?
A credential-based attack may take place in several ways. Some credentials management attacks may target pairs of usernames and passwords that were released in other data breaches, given the number of users that reuse their usernames or passwords on multiple sites. Called Credential Stuffing, this form of automated brute-force attack is on the rise, due in part to the number of large-scale corporate password data breaches.
Another type of credentials management attack relies on exploiting vulnerabilities in the way passwords are encoded, stored, or managed by a web application, network, or software system. Risky development practices, like storing passwords in improperly-secured locations, storing credentials in clear text, storing user passwords using weak or reversible encryption schemes, or using hard-coded credentials, create vulnerabilities that can be exploited to recover users’ credentials that can be used to attack your application and other applications the user logs into.
Ask a Qualified AppSec Expert
Primary Ways Attackers Breach Credentials
There are several primary ways that attackers may exploit credentials management vulnerabilities:
- Unprotected storage of credentials, such as when passwords are stored in plaintext
- The use of hard-coded credentials to store passwords or cryptographic keys used for encrypting credential data, authentication, or communication information
- Insufficient protection authentication mechanisms, allowing unauthorized access by means of cross-site request forgery (CSRF), cross-site scripting (XSS), or other attacks
- Insufficient password security practices that allow for easier use of brute-force attacks or credential stuffing
- The use of hard-coded passwords for either inbound or outbound communication
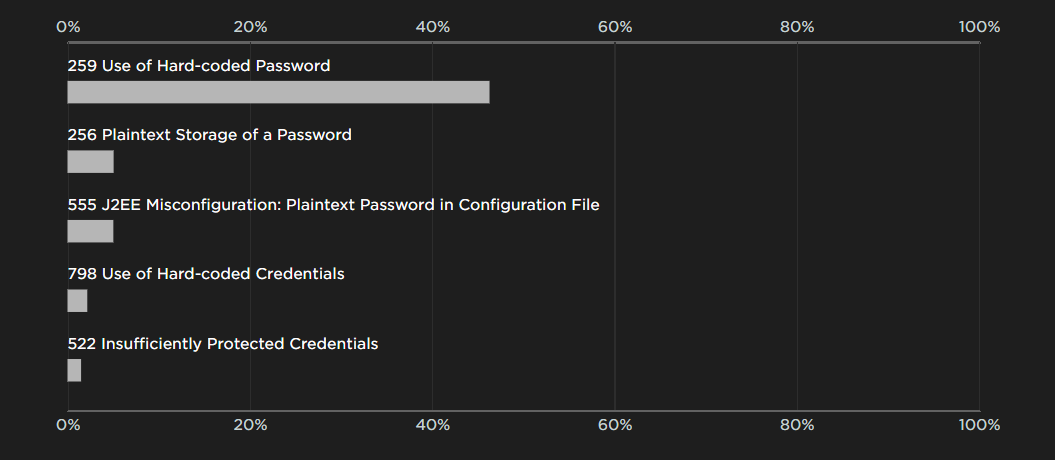
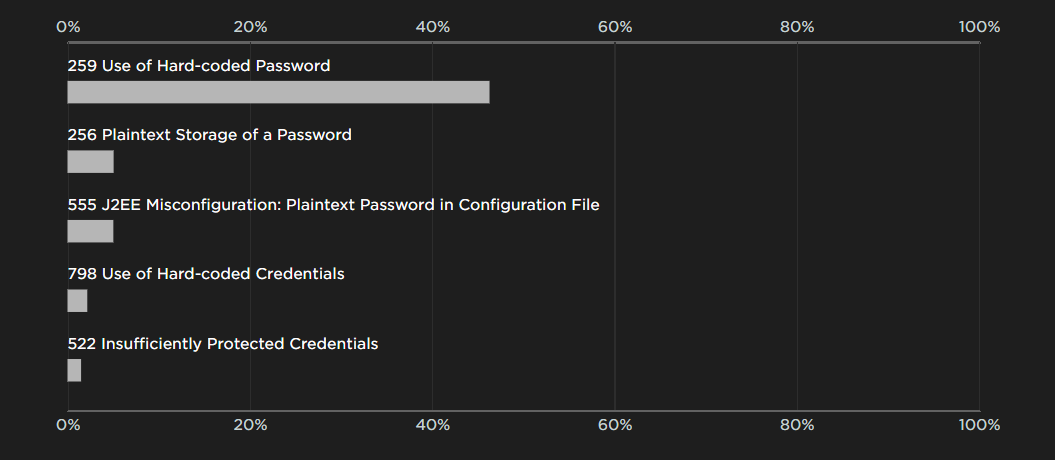
As this Veracode analysis points out, over 40% of software scanned by our tools contain some form of credentials management flaw. The most common is the use of hard-coded passwords, but all of these flaws present potential vulnerabilities. Veracode Dynamic Analysis can quickly discover application flaws such as credential management concerns in a production or pre-production environment, pointing developers toward solutions to remediate flaws.
How Credentials Management Attacks Work
Credential management vulnerabilities result when developers fail to build in essential protections. This may include a failure to encrypt password data or store credentials in an easily accessible file, or it may involve the use of hard-coded passwords that allow an attacker to bypass authentication requirements. In order to pull off a credential attack, intruders might intercept insecure data or use brute force methods. In some cases, such as with hard-coded passwords, attacks can be difficult for a system administrator to detect, and fixing a flaw can prove challenging. In fact, in some cases, it may be necessary to disable a product or site entirely. A Veracode analysis of static scan data indicated that credential vulnerabilities exist in 42 percent of applications.
Attack and Defense Examples
Example 1
This is an example of unprotected storage of credentials:
Properties prop = new Properties();
prop.load(new FileInputStream("config.properties"));
String password = prop.getProperty("password");
DriverManager.getConnection(url, usr, password);
This code reads a password from a properties file and uses the password to connect to a database. Although this code will run correctly, someone with access to the config.properties file can read the value of a password. This might include an employee who uses this information to breach the system.
Example 2
This is an example of the use of a hard-coded password vulnerability in Java:
int VerifyAdmin(String password) {
if (!password.equals("Mew!")) {
return(0)
}
//Diagnostic Mode
return(1);
}
The problem with this code is that every instance of this program can be placed into diagnostic mode using the same password. Making matters worse, a binary-only distribution of the program makes it extremely difficult to change the password or disable its “functionality.”
Example 3
This is an example in PHP of insufficiently protected credentials:
$user = $_GET['user'];
$pass = $_GET['pass'];
$checkpass = $_GET['checkpass'];
if ($pass == $checkpass) {
SetUserPassword($user, $pass);
}
The above code alters a user’s password. Once the code confirms that the user entered the same password twice, it provides access to the account. It doesn’t check the identity of the user to ensure that it’s the same person. This allows an attacker to take over the account.
Example 4
This is an example of a hard-coded credentials attack:
int VerifyAdmin(String password) {
if (password.Equals("68af404b513073584c4b6f22b6c63e6b")) {
Console.WriteLine("Entering Diagnostic Mode...");
return(1);
}
Console.WriteLine("Incorrect Password!");
return(0);
}
This example demonstrates how a cryptographic key is hard-coded into a string value that’s compared to the password. An attacker who views this code can compromise the system.
What Is the Best Way to Handle Passwords to Prevent a Credentials Management Vulnerability?
Best practices involve building in essential protections to mitigate and remediate flaws and prevent them from becoming vulnerabilities. It is important to avoid the use of hard-coded passwords or the storage of credentials in easy-to-locate areas. All authentication communication should be encrypted, without the use of hard-coded encryption keys.
Credentials like passwords and tokens, which the application uses to log into API’s and other services, need to be stored in a recoverable but secure way. Use credential management and key management systems to ensure proper storage of “outgoing” passwords. Encrypting them in a proper management system designed for this very purpose will help prevent credentials management vulnerabilities.
For “incoming” passwords that are used in authentication, utilize a directory or authentication service. Be sure to properly one-way hash and salt passwords using a scheme like bcrypt, scrypt, or Argon2. Incoming credentials should never be stored; only the digest from a tunable-work-factor password hash function with unique random salts should ever be stored.
How Do You Prevent Credentials Management Flaws?
Developers may use multiple tools to prevent credentials management flaws. Strengthening the method of authentication used by, for example, opting for multifactor authentication, can provide a strong defense against brute-force attacks. While multifactor authentication can provide a significant barrier to password attacks, it is not always practical or feasible, especially for non-sensitive access points.
Other approaches may also harden your login systems against automated attacks in particular, such as account lockouts or CAPTCHA challenges after a certain number of failed logins. Alternate, non-password identity verification may also be a preferred solution for some web applications, such as OAuth, OpenID, UAF, or SAML(Security Assertion Markup Language).
When passwords are still the best choice, it can also be helpful to limit permissions given to users. For example, employees given permissions to browse through entire file servers and directories may obtain access to secure, identifiable, or compromising information. If those employees do not need this access for their work, they should not have it. Excessive permissions controls may create barriers for users, but wise permissions control can help prevent either deliberate or inadvertent compromise of sensitive data.
Creating a strong password policy in your organization, including forbidding passwords found in popular data breaches or well-known weak passwords o, or encouraging the use of long randomly generated passwords along with password managers can increase security and help prevent credentials management vulnerabilities.
How Do You Remediate Code with Credentials Management Vulnerabilities?
While some languages do require source submission as there is no binary to submit, Veracode Static Analysis can identify credential management flaws and potential vulnerabilities for most languages in your application software (including third-party components) without examining the source code. This analysis can provide developers with information about exactly where and how to repair and remediate code vulnerabilities.
Wherever hard-coded credentials are found, they are a security flaw. This type of design error has been particularly publicized in the growing Internet of Things (IoT) space, where connected devices may be easily controlled with a limited list of hard-coded usernames and passwords. Avoiding and removing hard-coded credentials can provide greater safety for networked devices of all kinds.
Credential storage should also be examined. Authentication communication must be secure, but storage must be equally secure. Plaintext credentials, insecure hashing, and improper salt functions could introduce flaws.
Veracode Can Help You Prevent Credentials Management Attacks
Veracode Dynamic Analysis can safely, accurately, and quickly discover web application flaws, including credential management, in running web applications, in either production or pre-production environments.
Veracode Static Analysis can accurately identify credential management vulnerabilities and other flaws in your application and its third-party components and tell your developers exactly where and how to repair them, all without ever looking at the source code.
Our cloud-based Application Analysis can manage application security, avoiding and repairing credentials management and other security flaws. Veracode Security Labs provide advanced developer training that gives developers the knowledge to avoid creating credentials management flaws and produce compliant code from the start.

Secure Coding Handbook
A developer’s guide to delivering safer code faster in the cloud and on premises.