Explorer Resources Hub
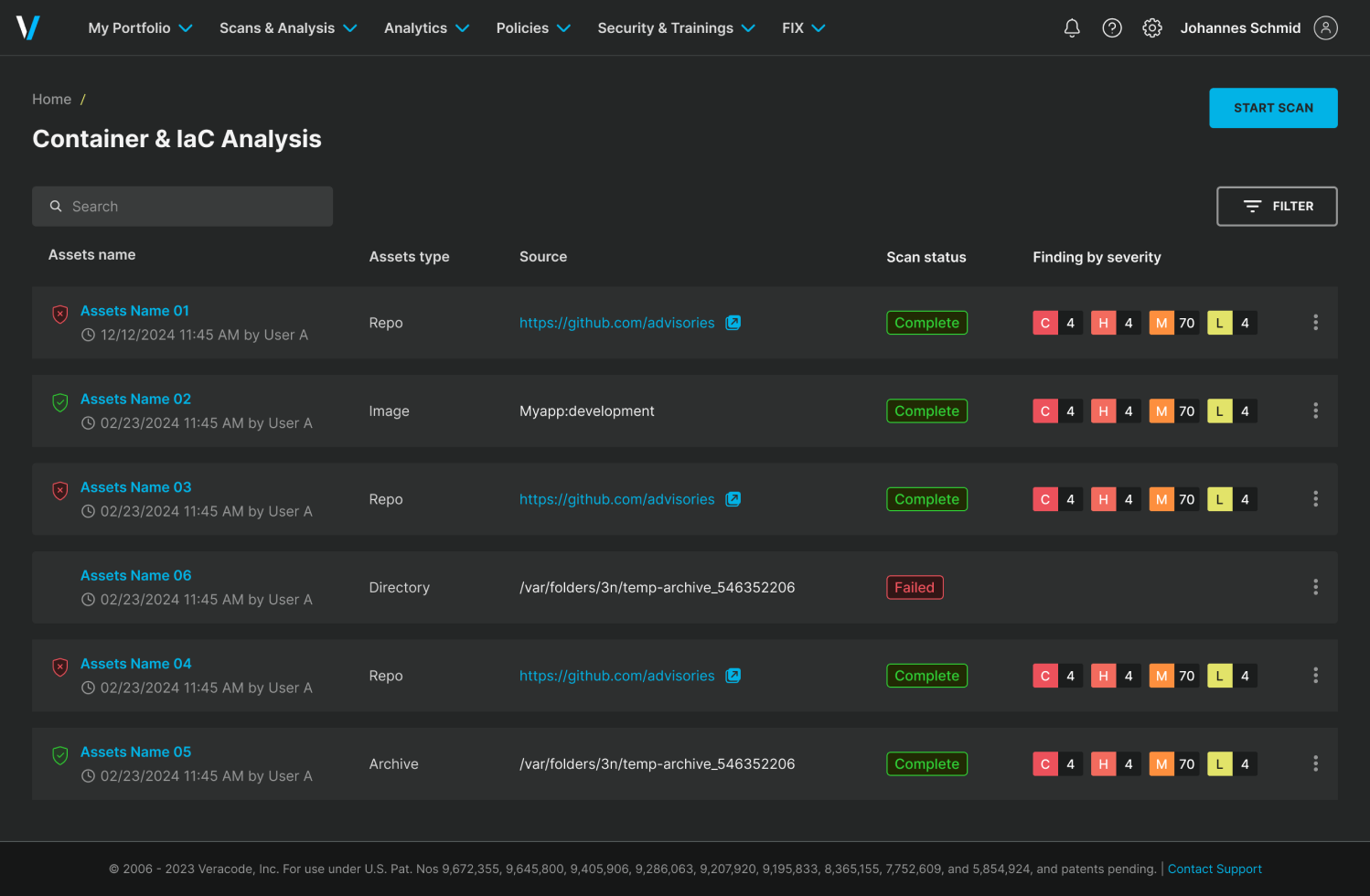
Image Vulnerabilities
Find vulnerabilities in your container images
IaC Misconfigurations
Spot insecure deployments due to infrastructure as code misconfigurations
Exposed Secrets
Find exposed API keys, passwords or secrets
Extra Features You’ll Love
Secure Containers and IaC with Proactive,
Scalable Scanning
Automate vulnerability detection, compliance, and remediation for containers in your CI/CD pipelines, ensuring seamless, cloud-native security.
Proactive Vulnerability Detection
Scan container images and IaC templates early in the development cycle to catch and address issues before they reach production.
Seamless DevOps Integration
Incorporate container and IaC scanning directly into existing CI/CD pipelines, ensuring security checks happen automatically with each build.
Policy-driven Compliance
Enforce internal and industry standards with customizable policies, enabling teams to maintain compliance across cloud-native environments.
Actionable Remediation Guidance
Receive detailed fix recommendations and best-practice insights for misconfigurations and vulnerabilities, accelerating resolution.
Centralized Visibility & Reporting
Track container and IaC security posture from a single platform, streamlining oversight and simplifying audits.
Scalability for Modern Environments
Leverage a cloud-native platform designed to handle dynamic and distributed infrastructures, ensuring uninterrupted scanning for all your containers and IaC assets.
Integrate Container Security into Your Pipeline Seamlessly
Provide developer-friendly tools to identify and mitigate vulnerabilities early, ensuring secure and compliant containerized applications.
Get Started Today