What is a Man-in-the-Middle Attack?
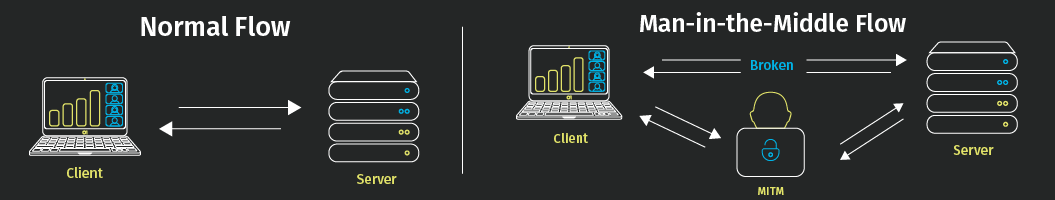
A Man-in-the-Middle (MITM) attack is a cyber threat where an unauthorized party intercepts and potentially alters communications between two intended participants, without their awareness. The attacker positions themselves between the victim and a legitimate service, acting as a covert conduit to observe, steal, or manipulate information.
MITM attacks exploit the real-time nature of network traffic, enabling attackers to perform unauthorized actions while appearing invisible to both sides of the conversation. This makes the detection of these attacks challenging, especially when strong security controls are not in place.
How Do Man-in-the-Middle Attacks Work?
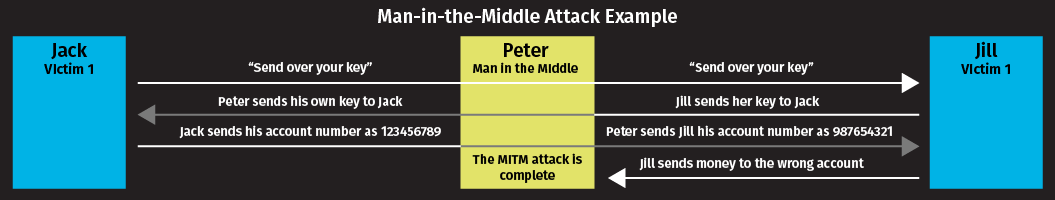
MITM attacks take advantage of weaknesses in communication protocols or network configurations. Attackers insert themselves into active connections, impersonating each participant while maintaining a legitimate-appearing exchange. This allows them to access sensitive information, modify data in transit, or inject malicious content.
Common characteristics of Man-in-the-Middle attacks:
- Session hijacking: Taking over active sessions to access user information or resources.
- Real-time interception: Capturing and, if desired, modifying data moving between parties.
- Dual impersonation: Pretending to be each party to the other, maintaining the illusion of legitimate communication.
- Stealth techniques: Employing methods to avoid detection, such as traffic redirection or encryption downgrade.
The process can be compared to the “telephone game,” where messages can be changed as they pass between individuals. The difference: in Man-in-the-Middle attacks, alteration is intentional and malicious.
Types of Man-in-the-Middle Attacks
Data Interception
How it works:
- The attacker monitors network traffic using packet capture tools.
- When a user submits login credentials or sensitive information, the attacker intercepts them.
- Users may be directed to fraudulent sites imitating trusted brands.
- Attackers leverage stolen data for unauthorized access or further fraud.
Financial Account Takeover
How it works:
- Attackers set up spoofed services to mimic banks or payment portals.
- They use intercepted credentials or session tokens to access victims’ accounts.
- Attackers relay information between the victim and legitimate institution, keeping the victim unaware.
- This enables fraudulent transfers or disclosure of confidential financial data.
Real-World Man-in-the-Middle Attack Examples
DigiNotar Certificate Authority Breach (2011)
Dutch certificate authority DigiNotar was compromised, leading to the issuance of fraudulent certificates for major websites, including Google and Skype. Attackers used these certificates to conduct large-scale MITM attacks, redirecting users to malicious servers that appeared legitimate. The event compromised user security significantly and resulted in DigiNotar’s bankruptcy.
Equifax Mobile App Vulnerability (2017)
In 2017, Equifax temporarily removed certain mobile applications after researchers discovered inconsistent implementation of HTTPS encryption. Weaknesses in certificate validation could allow attackers to intercept traffic, exposing user data to MITM threats. This case exemplifies the risks of improper encryption in high-value applications.
What Makes Systems Vulnerable to Man-in-the-Middle Attacks?
Several factors can expose systems and users to MITM risks:
- Unencrypted connections: Data transmitted over HTTP or unsecured protocols is easily intercepted.
- Weak certificate validation: Failing to verify certificates correctly enables attackers to use fraudulent credentials.
- Public Wi-Fi networks: Open or poorly secured wireless networks provide attackers an opportunity to intercept communications.
- Compromised certificates: If trusted certificates are issued to attackers or stolen, secure connections can be subverted.
- Outdated security protocols: Relying on deprecated or misconfigured encryption protocols increases exposure.
Environments handling sensitive data—such as financial services, login portals, and enterprise systems—are frequent targets.
How to Prevent Man-in-the-Middle Attacks
For Organizations
Enforce Strong Encryption
- Require HTTPS with strict TLS configurations for all communications.
- Validate certificates with industry best practices.
- Use certificate pinning in mobile and web apps to mitigate fraudulent certificate risks.
- Stay up-to-date on deprecating outdated protocols (e.g., SSL, early TLS versions).
Adopt Secure Software Development Practices
- Integrate security testing throughout the SDLC, including dynamic and static analysis.
- Conduct regular third-party penetration testing focused on authentication, encryption, and session management.
- Validate input and output to mitigate injection and session hijacking risks.
Enhance Network Security Measures
- Deploy intrusion detection and prevention systems to identify abnormal traffic patterns.
- Use mutual authentication for sensitive systems.
- Regularly audit digital certificates and revoke any that are unused or compromised.
For Users
Verify the Security of All Connections
- Ensure you only enter sensitive information on verified HTTPS websites.
- Heed browser warnings related to certificates or site identity; do not bypass them.
- Avoid performing sensitive tasks over public or untrusted Wi-Fi. If unavoidable, use a trusted VPN.
Maintain Vigilance
- Watch for unexpected login requests, pop-ups, or changes in website appearance.
- Monitor accounts for unauthorized transactions or security notifications.
- Keep devices, browsers, and applications updated to reduce exposure to known vulnerabilities.
Session Hijacking Techniques Related to Man-in-the-Middle Attacks
Man-in-the-Middle attacks are part of a wider set of session hijacking techniques, including:
Sniffing: Capturing data transmitted across networks using specialized software.
Sidejacking: Stealing unencrypted session cookies to usurp active sessions; a risk especially on unsecured Wi-Fi.
Evil Twin Attacks: Setting up rogue Wi-Fi access points that mimic legitimate networks, drawing users to connect and exposing traffic to interception.
Strengthen Your Defense Against Man-in-the-Middle Attacks
A robust strategy to prevent MITM attacks requires a commitment to secure coding, network hardening, and continuous monitoring. Integrate security requirements into every stage of software development and conduct rigorous testing to identify and address vulnerabilities early.
Veracode’s cloud-based platform empowers development and security teams to detect and remediate vulnerabilities—including those that expose applications to MITM risks. Our dynamic and static analysis solutions help you safeguard enterprise applications and customer data against evolving threat actors.
Frequently Asked Questions
How can I tell if I’m experiencing a Man-in-the-Middle attack?
Alert signs may include browser certificate warnings, unexpected website redirects, login prompts from unknown sources, or slower-than-normal connections. If in doubt, verify the site or request directly through official channels.
Are mobile apps vulnerable to Man-in-the-Middle attacks?
Yes. Mobile applications are susceptible, especially when lacking proper HTTPS enforcement or certificate validation. The Equifax incident highlights the necessity of stringent encryption in mobile platforms.
Can MITM attacks occur on encrypted connections?
Encryption provides strong protection, but attacks are still possible if certificate validation is weak, if certificates are compromised, or if attackers use downgrade techniques such as SSL stripping. Maintain rigorous certificate management to reduce this risk.
What should I do if I suspect a Man-in-the-Middle attack?
Disconnect from the network immediately. Change passwords for affected accounts, notify your IT or security team, and closely monitor account activity. For incidents involving financial or personal data, report to relevant authorities or your institution’s support channels.
