PTaaS resources hub
Trusted expertise
Certified, experienced testers identify real-world risk
Dedicated testing
Guaranteed testing, never driven by incentives
Flexible services
Service packages tailored to meet your business needs
Extra features you’ll love
Test like attackers. Secure like experts.
Our core functionality combines real-world risk insight with deep security expertise and tailored consulting, keeping you agile and prepared to meet evolving security and compliance demands.
Consistent testing
Your dedicated penetration tester will provide guaranteed testing, validated results and personalized consulting.
Automated scheduling
Set up recurring tests on a customizable schedule to stay ahead of compliance and customer needs.
Predictable pricing
Flexible pricing models scale with your application’s growth, code updates, and new releases.
Regulatory compliance
Meet penetration testing compliance requirements for PCI DSS, HIPAA, GDPR, and other regulations.
Actionable results
Get actionable, peer-reviewed feedback with Fix recommendations tailored to your unique security landscape.
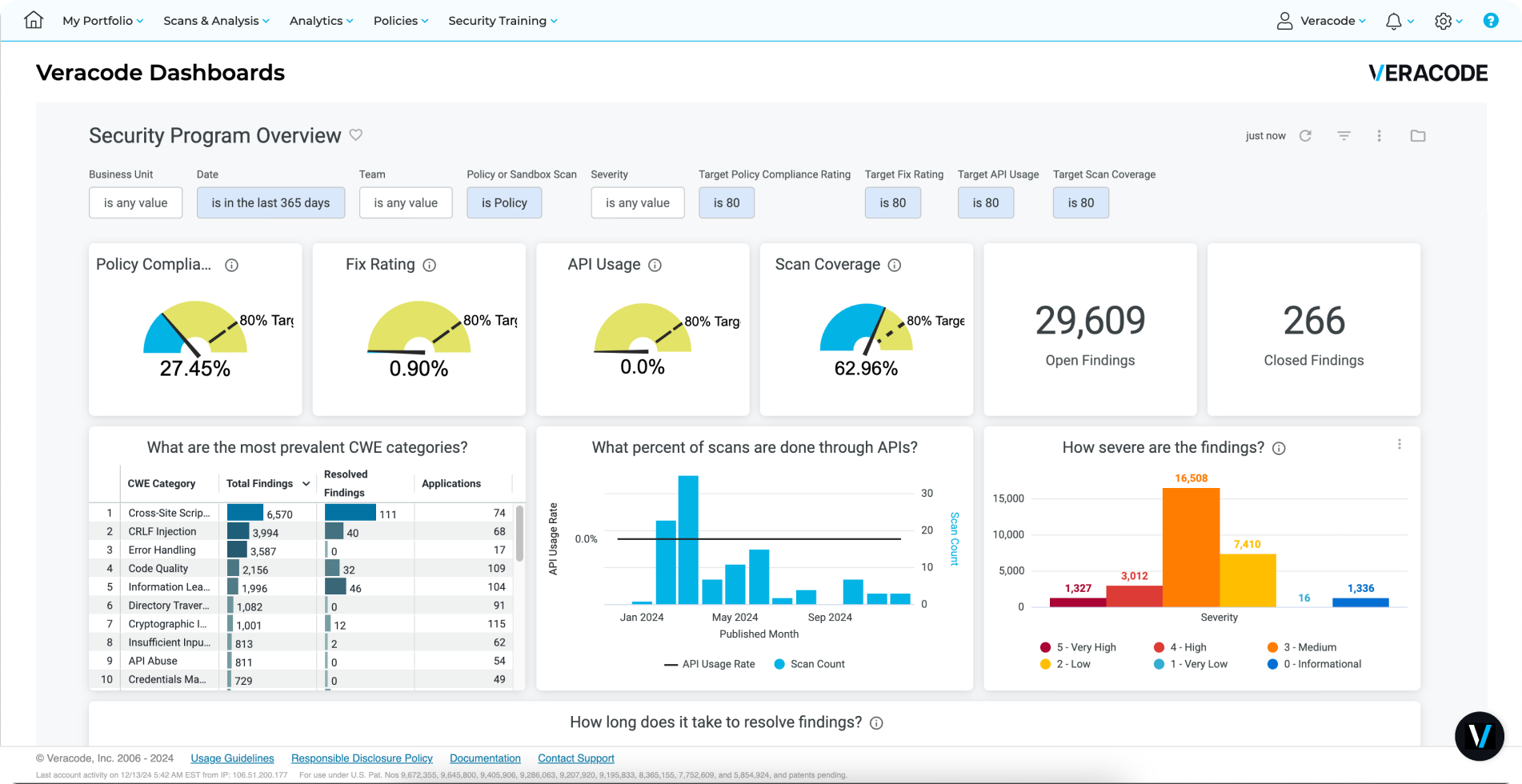
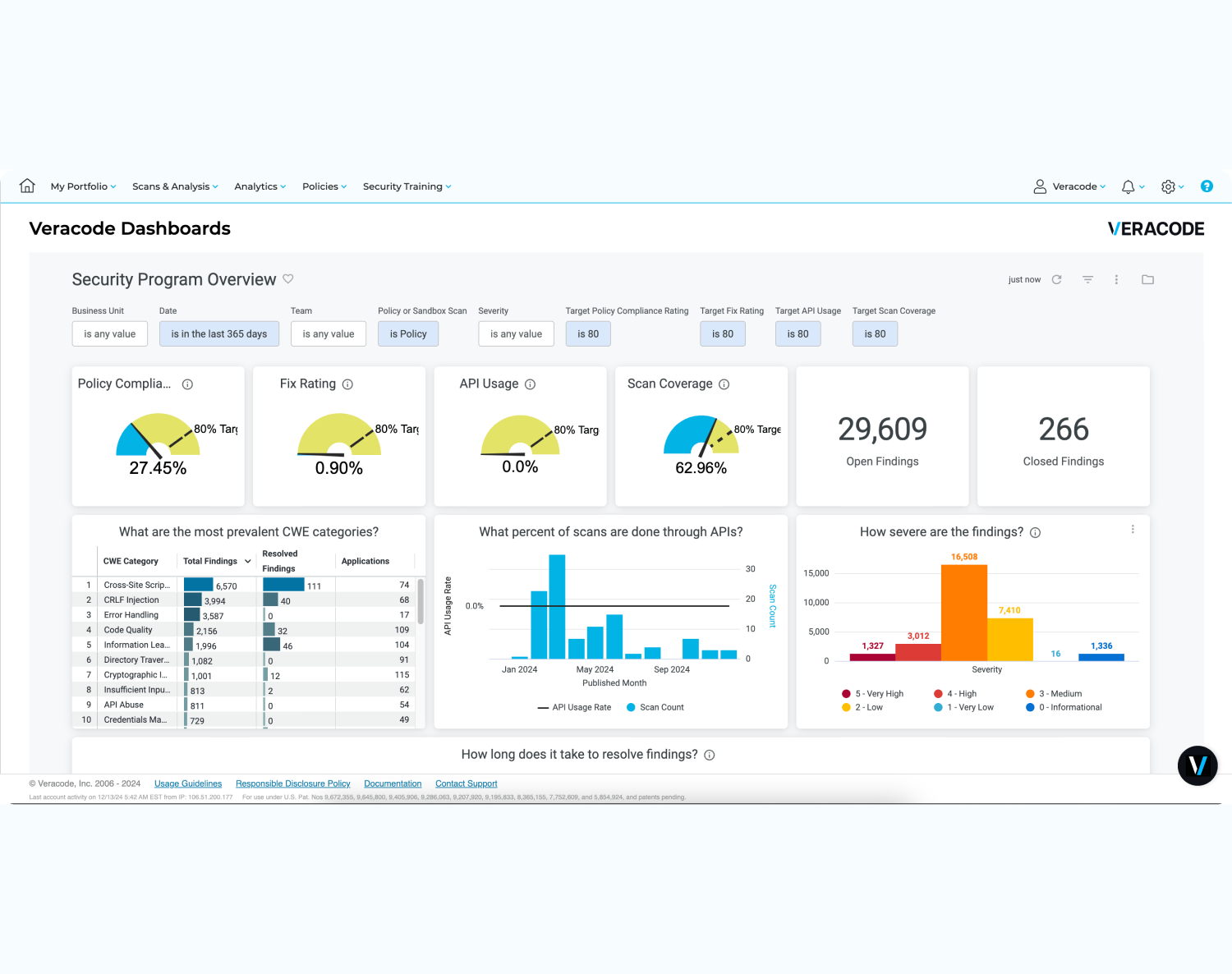
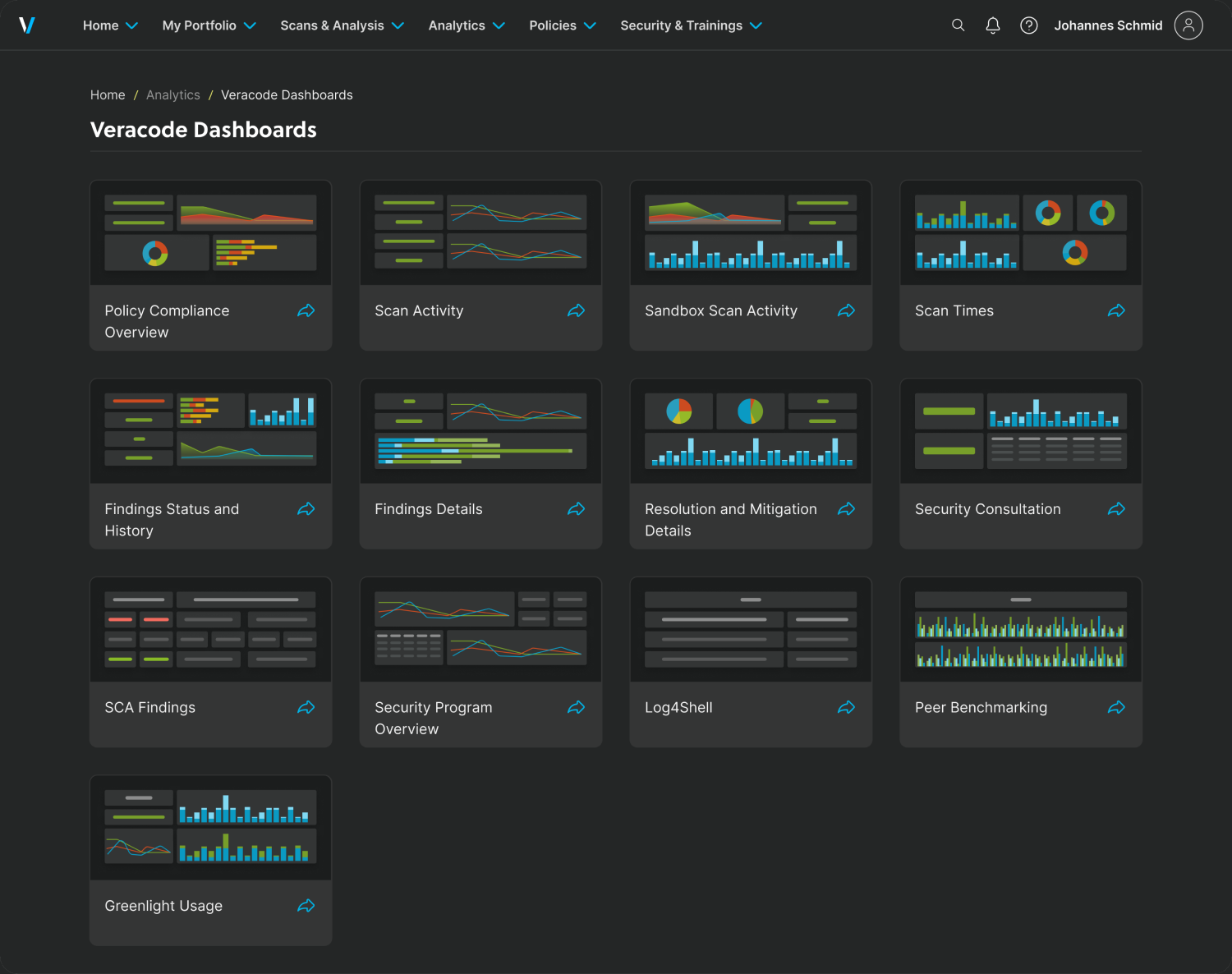
Centralized platform
View results alongside automated security tests to get a holistic, multi-faceted view of your attack surface
Uncover complex vulnerabilities with human insight
Identify complex vulnerabilities, gain personalized insight, streamline testing processes, ensure compliance and integrate security practices throughout development.
The Total Economic Impact of the Veracode Application Risk Management Platform
Increasing application risk management maturity has big financial outcomes: 20% revenue growth, reduced risk, increased productivity, and ROI within six months (Forrester Study).

Get started today
Harness the Power of Veracode
For secure, confident coding to identify
and fix vulnerabilities early.