Secure Your Software Supply Chain
Why Veracode Software Composition Analysis?
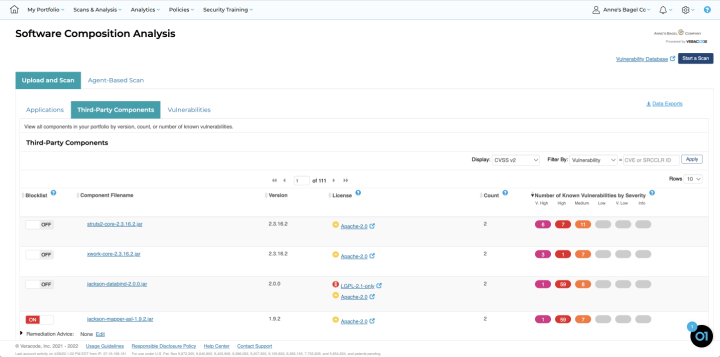
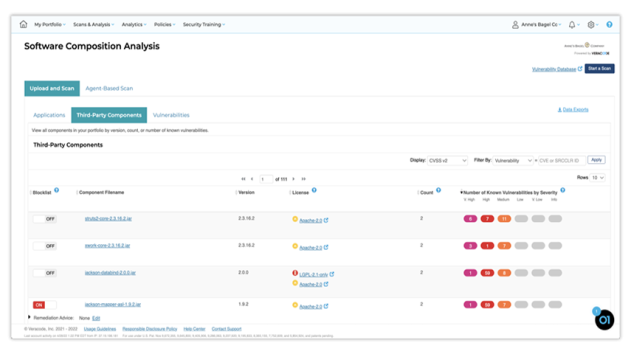
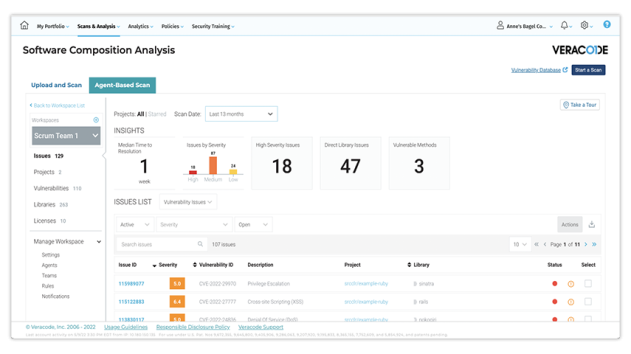
Veracode Software Composition Analysis Makes It Easy To ...
Features
Forrester Names Veracode a Strong Performer in SCA Wave
Veracode has been recognized in a report Forrester Research recently released, The Forrester Wave™: Software Composition Analysis, Q2 2023. The report helps security professionals select a software composition analysis (SCA) vendor that best fits their needs. The report, which evaluates 12 SCA vendors against 32 criteria, ranks Veracode as a Strong Performer.
Veracode is Trusted by 2,600 Companies Globally
Featured Resources