Regulatory frameworks play a crucial role in ensuring the resilience and security of organizations. One such regulation that has garnered significant attention is the Digital Operational Resilience Act (DORA). Here are the key aspects of DORA, as well as guidance for how to ensure compliance with it while measurably reducing risk to your business.
DORA Timeline and Overview
DORA, governed by three European authorities – the banking authority, the insurance and pension authority, and the securities and markets authority – is set to come into force on 17 January 2025. This act aims to establish security requirements for companies within the financial sector and their third-party service providers.
One driving force behind why you need to pay attention to DORA is that it’s a regulation and not a directive. A regulation means that come January 2025, it’s in effect without anything else needing to happen as far as being translated into laws; a directive would mean it needs another round of lawmaking to follow the directive’s direction.
Keep in mind: this regulation doesn’t introduce anything new in explaining best practices for digital resilience; it just adds the “or else” to what has already been found to be beneficial.
The 5 Pillars of DORA
DORA is structured around five pillars or sections, each addressing specific areas of digital resilience. Let’s explore these pillars before looking at how they relate to software security.
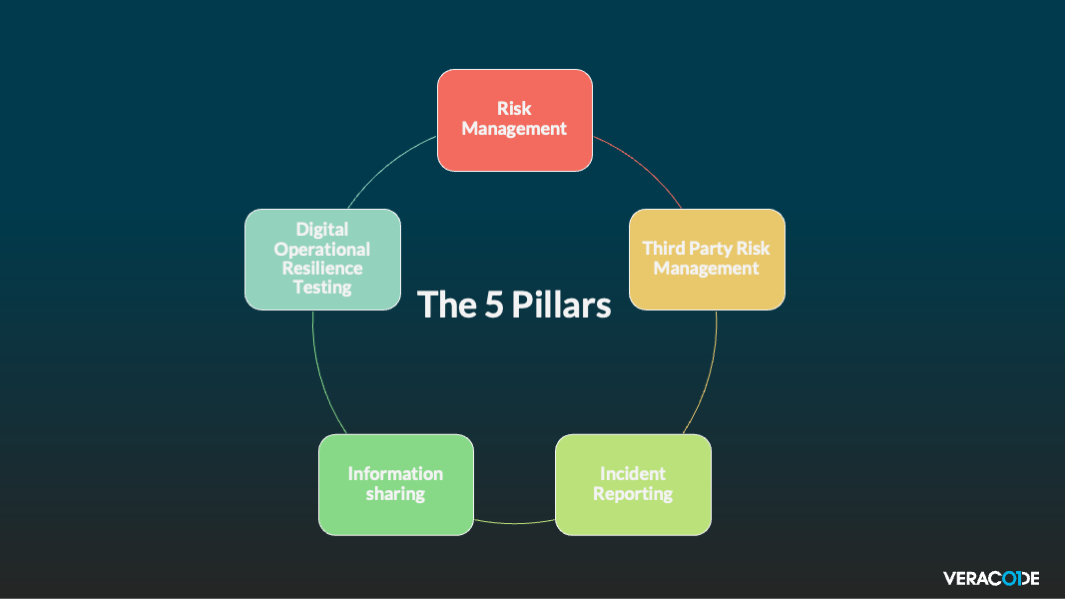
- Risk Management: The risk management pillar focuses on the identification, assessment, and mitigation of risks associated with operational resilience. Entities must have internal governance and control frameworks that ensure the effective and prudent management of all Information and Communications Technology (ICT) risks to bring about a high level of operational resilience.
- Third-Party Risk Management: This pillar emphasizes the need for organizations to assess and manage the risks posed by their third-party service providers. DORA defines a set of key principles for entities to achieve sound management of ICT third-party risks and engage in a robust contractual relationship with ICT third-party service providers.
- Incident Reporting: Incident reporting is a critical aspect of DORA, requiring organizations to promptly report any significant operational disruptions or cyber incidents. As part of their ICT-related incidents management process, entities must define, establish, and implement a management process to detect, manage, and notify them.
- Information Sharing: The information sharing pillar encourages collaboration and the exchange of cyber threat intelligence among organizations. DORA promotes information-sharing arrangements among financial entities with a view to enhancing digital operational resilience, by raising awareness of cyber threat information and intelligence, including indicators of compromise, tactics, and cybersecurity alerts.
- Digital Operational Resilience Testing: The final pillar of DORA emphasizes the importance of a programmatic approach of regular testing to ensure the operational resilience of organizations. As part of the ICT risk management framework, entities have to establish, maintain, and regularly review a sound and comprehensive digital operational resilience programme.
Software Security and DORA Compliance
For organizations involved in finance, insurance, and customer data within the EU, DORA compliance is crucial. As a trusted software security provider, Veracode can play a significant role in helping organizations navigate DORA regulations.
Veracode’s expertise in application security testing aligns with the risk management and digital operational resilience testing pillars of DORA. Our comprehensive testing capabilities, including Static Analysis (SAST), Dynamic Analysis (DAST), Penetration Testing (PTaaS), and Software Composition Analysis (SCA), can assist organizations in fulfilling the security requirements for risk assessment processes outlined in DORA.
Risk management needs data, and this data comes from a programmatic approach to application security in a platform with robust analytics. Our platform can give you quick access to information about when an app was scanned last, what the results of the scan were, how many open and closed findings you have, benchmarks against peers in your industry, and more.
Furthermore, Veracode’s vulnerability intelligence and threat research can contribute to the information sharing pillar of DORA. By staying ahead of emerging vulnerabilities and sharing this knowledge with our customers, we can help them enhance their threat intelligence capabilities and strengthen their overall security posture.
Compliance Aided by the Power of AI
One final comment about risk management and vulnerability testing: testing alone is insufficient for reducing risk. Testing must be accompanied by addressing the results of the tests. This means fixing the findings from the scan that pose risk. Manual vulnerability fixing is a tedious task, but you can read more about AI-assisted remediation in our new whitepaper, A Smarter Way to Secure Apps: The Power of Veracode Fix.



