+
Integrations
+
Languages Supported
+
Trillion Lines of Code scanned
%
False-Positive Rate
Great Code Is Secure Code
Veracode’s automated security tools deliver fast, accurate, and reliable results, without the noise of false positives.
Our tools integrate into existing development toolchains without adding needless steps to the software lifecycle, so security becomes an invisible part of the process. Quickly find and fix security flaws while you code, so you can create secure software with greater confidence and speed.
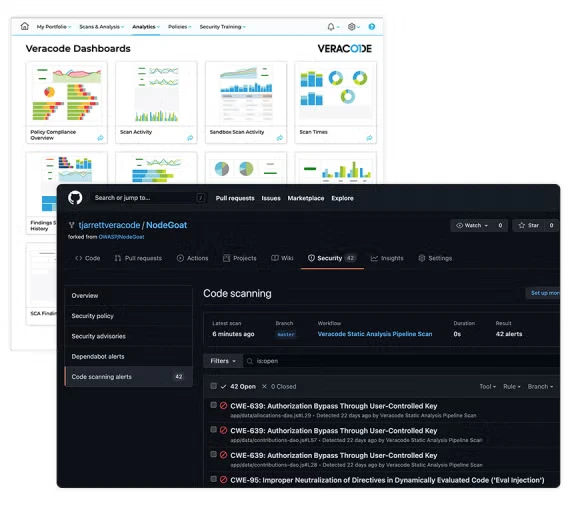
Veracode Static Analysis
Ensure the code you write, or assemble, meets company security standards. Our scalable cloud-native solution allows you to quickly find security defects across a broad range of languages and frameworks, throughout the development process.
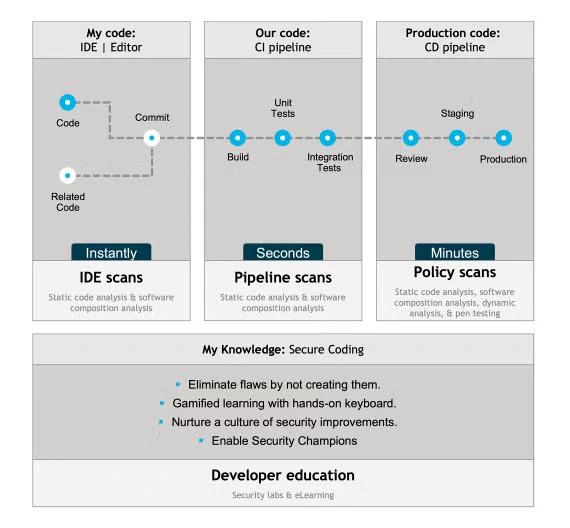
Veracode Static Analysis IDE Scan
Find security defects in your code instantly. Scan code as you write, and get in-context remediation guidance automatically – so you can fix flaws before they ever get committed.

Veracode Static Analysis Pipeline Scan
A static scan capability that embeds directly into your favorite CI/CD development tools for seamless AppSec scanning of first- and third-party code.
You can run the Veracode Static Analysis Pipeline Scan on every build, with a median scan time of 90 seconds. You can also configure it to break the build if new security issues are found.
Veracode Software Composition Analysis
Speed up development, without the downside risk of open source vulnerabilities. Use the same scan you’ve set up for static analysis to quickly identify vulnerable components.

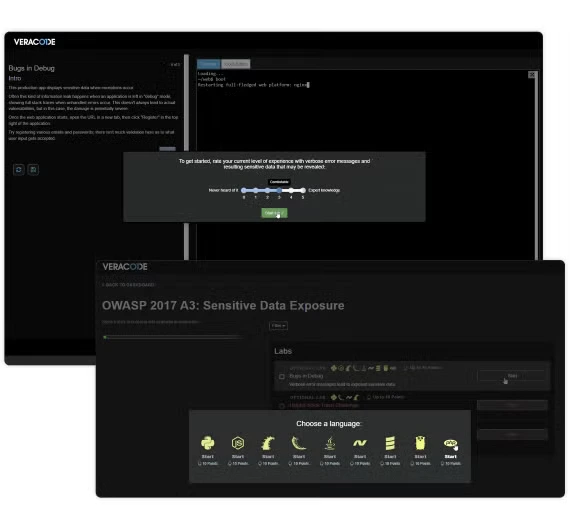
Veracode Secure Code Training
Hone your secure coding skills to continue producing high-quality code with training that meets your learning style. Try the hands-on approach with Veracode Security Labs, access on-demand videos with Veracode eLearning, or contact us for an expert consultation.