Static Application Security Testing (SAST) tools present a significant opportunity for organizations looking to reduce application security risk. However, not all workflows or tools are created equal. Using the right SAST tools at the right times, you can seamlessly integrate and scale security workflows throughout the software development lifecycle (SDLC). In this post, we’ll walk through examples of how easily you can work with Veracode’s SAST tools for first-party and third-party code scanning when using Azure DevOps and Visual Studio – and the different plugins available.
Ticket Follow Up
Let’s start where all developers’ workdays begin: the ticketing system. In this scenario, it’s the Azure DevOps Workboard, and the idea is that you have run a SAST policy scan. A Veracode policy scan effectively tests at the integration or systems level. Through integration, the tool can automatically generate security bug tickets inside of Azure DevOps based on scan results.
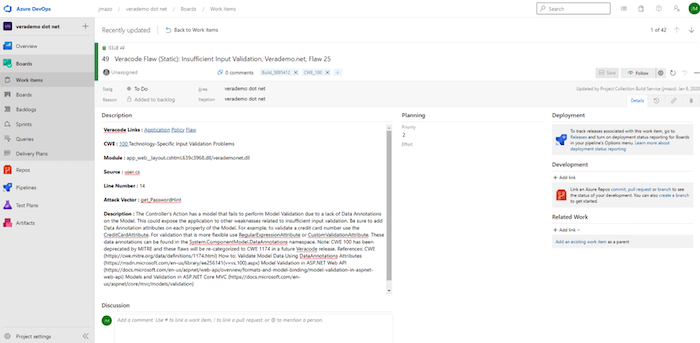
From the ticket, you can see several key elements. In the results list, you’ll find the specific flaw ID number. The flaw ID number is a unique identifier for each occurrence of a code weakness. Use this number to look up a flaw within the integrated development environment (IDE) and the Veracode Continuous Software Security Platform.
From the ticket, teams can also see the flaw’s source module. This information can help development managers identify which groups are associated with the affected code. The ticket will also feature the CWE ID. (CWE stands for Common Weakness Enumeration, which is a standard, community-supported list of software and hardware weakness types.) Finally, in the ticket, you will also be able to access information on the flaw and how to fix it.
IDE: Policy Results Access via Plugin
For those employing Veracode Static for Visual Studio, you can access scan results and begin addressing issues within Visual Studio. This plugin enables pulling the results of a policy scan directly into the Visual Studio IDE.
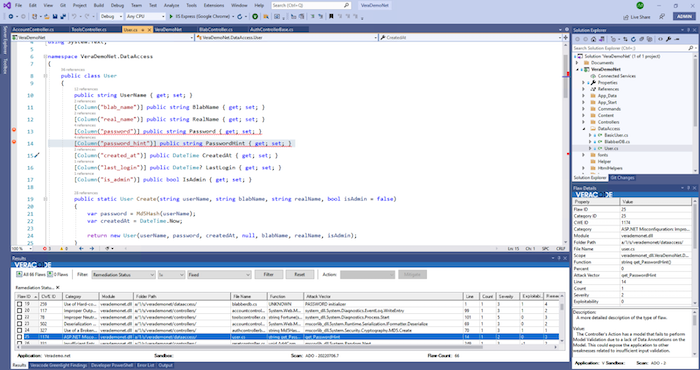
When you want to start addressing a flaw discovered, you can find the flaw ID and then access a description of the flaw and other intelligence that can aid in issue remediation or mitigation. From the list of flaws discovered, double-click on the flaw ID, and you will immediately be directed to the specific line of code that contains the issue.
It’s possible to do manual suppression through the mitigation workflow accessible on the Visual Studio screen. Those with permission to propose a finding can do so right in the IDE; authorized users can accept a proposed mitigation as well.
In Veracode Static for Visual Studio, just as in the Veracode Continuous Software Security Platform, teams can run scans and view details. Consequently, security and development teams will be able to work with different tools, while leveraging the same information. This gives these teams a standardized way to view and discuss findings.
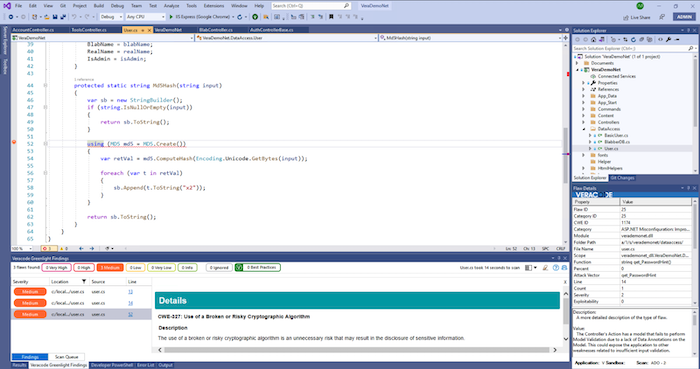
IDE: Greenlight Plugin
In addition to Veracode Static for Visual Studio, teams can also use the Greenlight plugin. Through this plugin, teams can do fast, unit-level tests. These unit-level tests help teams quickly address the “low hanging fruit,” the easy-to-tackle issues that get uncovered by unit tests. This plugin enables teams to do fast, repeated tests on modified code and verify whether the changes resolved the issue.
IDE: Software Composition Analysis
After you make changes to first-party code, you may also want to check and see if any vulnerabilities associated with third-party code may have been introduced. To ensure complete code coverage, run a scan using the Veracode Software Composition Analysis (SCA) CLI agent.
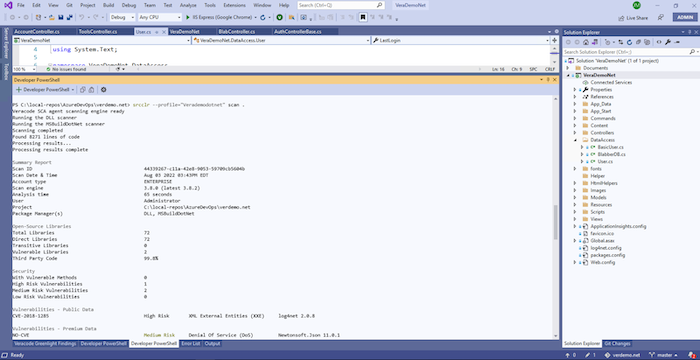
To do so, you would launch a developer console in your IDE, navigate to the repository, and run the scan command. The Veracode SCA scan will reveal any libraries that have vulnerable methods.
Within about one minute, you can see a list of Vulnerable Methods and identify which pose the highest risk to code. While there may be hundreds of vulnerabilities in libraries used, the solution enables you to identify whether code is actually invoking any of these flaws. Those flaws are what Veracode calls Vulnerable Methods.
If no Vulnerable Methods are discovered, commit the code to the repository. Once the code is committed, the Azure DevOps pipeline can detect the code change and automatically trigger a build and Veracode policy scan. If the code is fixed, the Azure DevOps ticket will be closed automatically, and it will also show up as closed in the Veracode Continuous Software Security Platform.
Security Labs
If a scan doesn’t come back as clean and you aren’t sure how to proceed, Security Labs can help.
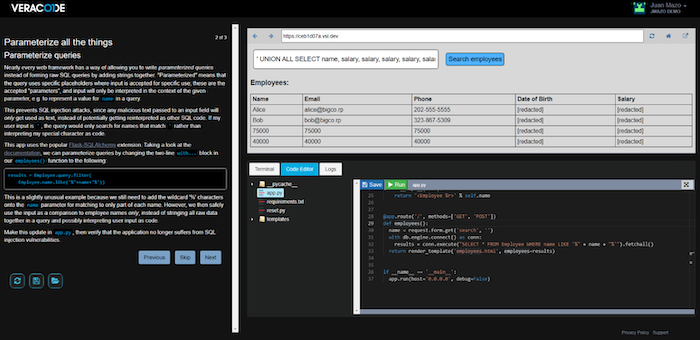
Security Labs can be viewed as just-in-time learning. Security Labs features targeted interactive sessions that teach secure coding practices and principles; you can modify and patch real apps in a sandbox environment. Security Labs includes hundreds of courses on numerous topics, including OWASP Top 10 vulnerabilities, GDPR, memory management APIs, mobile apps, and more. Security Labs offers coverage of .NET, PHP, JavaScript, Java, C, Ruby, Python, and other languages. Instead of scheduling time with a consultant or doing hours of research online, simply access Security Labs and, usually within fifteen minutes, learn how to patch a given piece of code.
Get Training or Assistance
Know that you’re not alone! There are a wide range of resources and services you can access:
- Application security consultants (ASCs). ASCs are seasoned professionals who are experts in both development and security. ASCs can provide targeted guidance, particularly in helping customers complete remediations. Customers can schedule a meeting with an ASC directly from their IDE or platform interface.
- Implementation support. Veracode can provide assistance with a range of efforts, including integrating with IDEs and setting up and refining CI/CD workflows.
- Community support. Customers can leverage community-developed integrations in Veracode GitHub or find help in the Veracode Community.
- Technical documentation. Customers can gain self-service access to technical documentation.
Conclusion
With Veracode solutions, development and security teams can identify and address flaws with unparalleled efficiency and speed. Through our solution plugins, developers can seamlessly learn about code flaws and address them, without having to leave their IDE of choice. At the same time, Veracode solutions help ensure developers and security teams are working from consistent, standardized flaw intelligence, so they can collaborate more effectively.
Check out the 6 Steps to Secure the SDLC eBook to learn more about integrating security at scale.



