APPLICATION SECURITY
Knowledge Base
Search Our Knowledge Base
SQL Injection: Vulnerabilities & SQL Injection Prevention
What is SQL Injection?
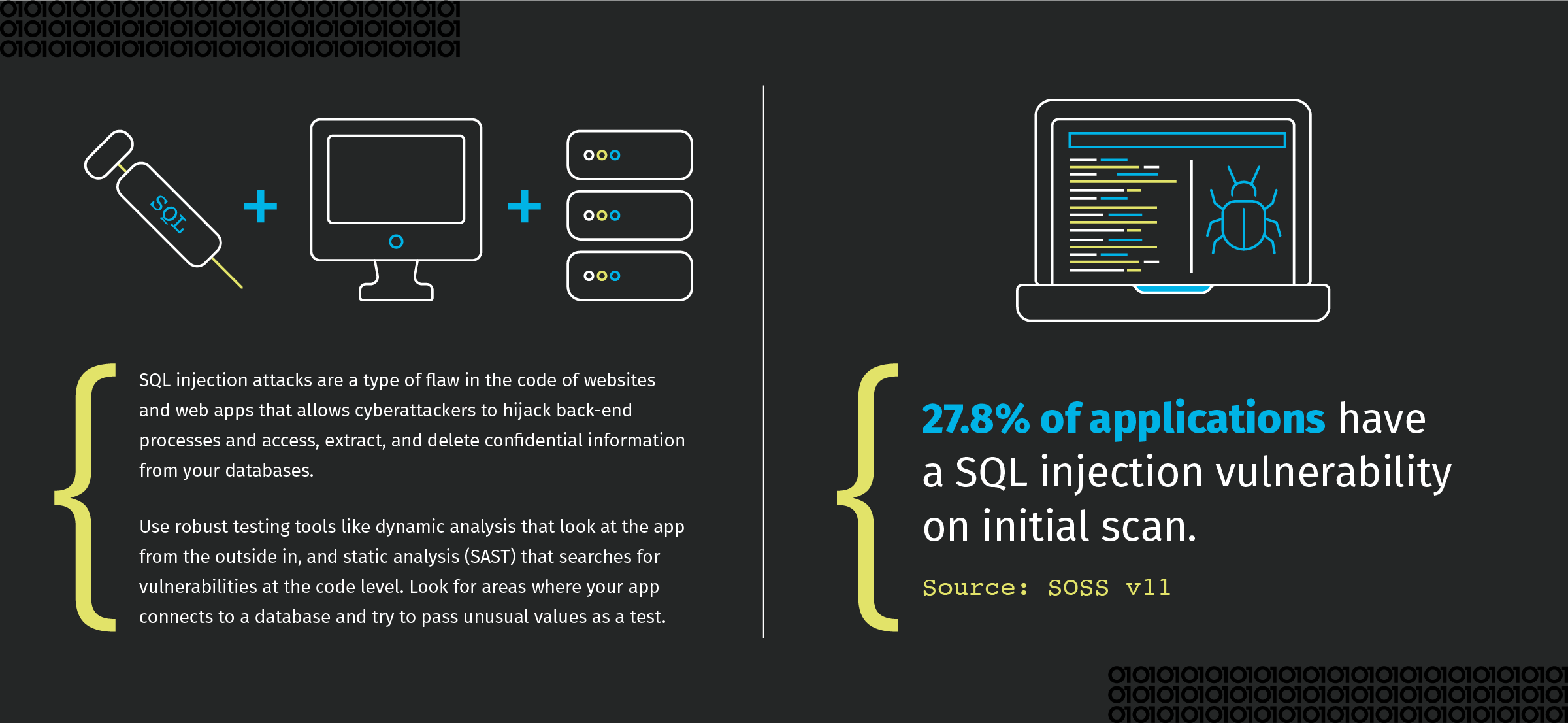
SQL injection attacks, also called SQLi attacks, are a type of vulnerability in the code of websites and web apps that allows attackers to hijack back-end processes and access, extract, and delete confidential information from your databases.
Although SQLi attacks can be damaging, they're easy to find and prevent if you know how. In this post, we'll teach you the basics of finding and neutralizing these vulnerabilities in your app's code.
What Is a SQL Injection Attack?
SQL, or Structured Query Language, is the standard language for interacting with relational databases. In apps and other types of programming, databases are used to store user data such as usernames and passwords. Databases are also often the most effective, secure solution for storing other types of data from public blog posts and comments to confidential bank account numbers.
SQL statements often use arguments to pass data from users into a secured database or vice versa. Unless the values in these user-supplied SQL arguments are secured by sanitizing or prepared statements, attackers can use the places where your app communicates with a database with a SQL argument to gain access to confidential information and other secured areas.
What Can Attackers Do With a SQL Injection Attack?
SQLi attacks make use of vulnerabilities in code at the point where it accesses a database. By hijacking this code, attackers are able to access, modify, and even delete secured data.
When SQLi attacks are successful, attackers can:
- Log in to an app or a website front end without a password.
- Access, extract, and delete stored data from secured databases.
- Create their own database records or modify existing records, opening the door for further attacks.
Anatomy of a SQL Injection Attack
In the reconnaissance stage, which entails research to identify and select targets, attackers will look for places in your app where they can pass unexpected values to SQL statements. Suppressing error messages simply isn’t enough; common methods for discovering SQL vulnerabilities include adding single quotes and semicolons into user input data and looking for error messages that return information about database structure and naming schemes.
It isn’t as though you’re always going up against a person that you simply need to outsmart; SQL injection attacks are easy to automate, which means you need the best defense in both brainpower and scanning tools. Once they have found vulnerabilities in your app, attackers will create their own SQL statements and use them to manipulate your app's behavior. If their attack is successful, attackers will be able to gain access to confidential data, administrative functions, or other secured areas of your app.
Case Studies and Consequences
Because of their simplicity, SQLi attacks are common. They can have devastating consequences for you and your users.
In 2016, an anonymous whistleblower leaked 11.5 million confidential documents from Mossack Fonseca, a Panamanian law firm. Attackers were able to exploit SQL statements in the firm's content management system and other insecure network architecture to access the firm's customer database and download confidential files. The release of these documents was not only embarrassing, but it had significant legal consequences for customers as well.
In 2009, Russian and U.S. nationals used SQLi attacks to gain access to 160 million credit card numbers from Heartland Payment Systems in what was at the time the largest breach of financial information. The attackers sold the stolen card numbers on the black market, and other criminals quickly ran up bills in the hundreds of millions of dollars, harming corporations and individuals alike.
Even MySQL, a popular SQL provider, suffered from an SQLi attack to its website in 2011 that released hundreds of usernames and password hashes. The fact that an SQL provider can fall victim to SQLi attacks shows that no one is immune, and attackers will do their best to take advantage of insecure code.
Preventing SQL Injection Attacks
Despite the significant dangers posed by SQLi attacks, they're easy to prevent once you learn some secure coding best practices that include foundational procedures:
- Discover vulnerabilities
- Repair vulnerabilities
- Remediate vulnerabilities
- Mitigate impact
Testing is the key to discovering vulnerabilities in your code. Opt for robust tools like dynamic analysis (DAST) that looks at the app from the outside in as an attacker would, and static analysis tools (SAST) that looks for vulnerabilities at the code level. Look for areas where your app connects to a database and try to pass it unusual values. For example, if you put in a value that contains a single quote, does your program treat that character as user data, or does it treat it as code? If you include a tautological test (like ' OR '1=1') in your input, are you able to gain access as though you entered a valid password?
Once you have discovered vulnerabilities, it's time to repair them. The best way to do this is by using parameters any time you need to make SQL queries to a database, entering placeholder values in your statements and then passing user-inputted values to the statements at the time of execution. If your programming language does not support parameters, you can remediate your code by sanitizing or escaping input before passing it to a database. This lets your app know that user input is data rather than code it should execute.
Mitigation is also an important process to help reduce risk, but without addressing the underlying flaw. As an example, rather than looking to your app's code, you might mitigate a flaw by examining database accounts used by your app and making sure that they have the smallest amount of privileges needed to read or insert data to your database.
Smart Developers, Secure Development
SQLi attacks can have severe consequences once threat actors have control, from your app or website going down to your customers' confidential data being leaked.
Fortunately, SQLi attacks are easy to protect against. You need to look for vulnerabilities where attackers might inject their own SQL code and then repair those vulnerabilities using prepared statements, ORMS, and other strategies. If prepared statements are unavailable, vulnerabilities can be remediated by sanitizing or escaping user input before passing it to a database in a SQL query. Finally, enacting smart database access privileges can mitigate the number and severity of SQLi attacks before your app ever gets to executing queries.
Application development means thinking about vulnerabilities and security best practices at every step of the process. Download our SQL injection cheat sheet, and learn more about preventing dangerous vulnerabilities like SQL injection in our Secure Coding Best Practices Handbook.