Featured Resources
M +
Applications Scanned
M +
Software Flaws Fixed
T +
Code Lines Scanned
% <
False-Positive Rate
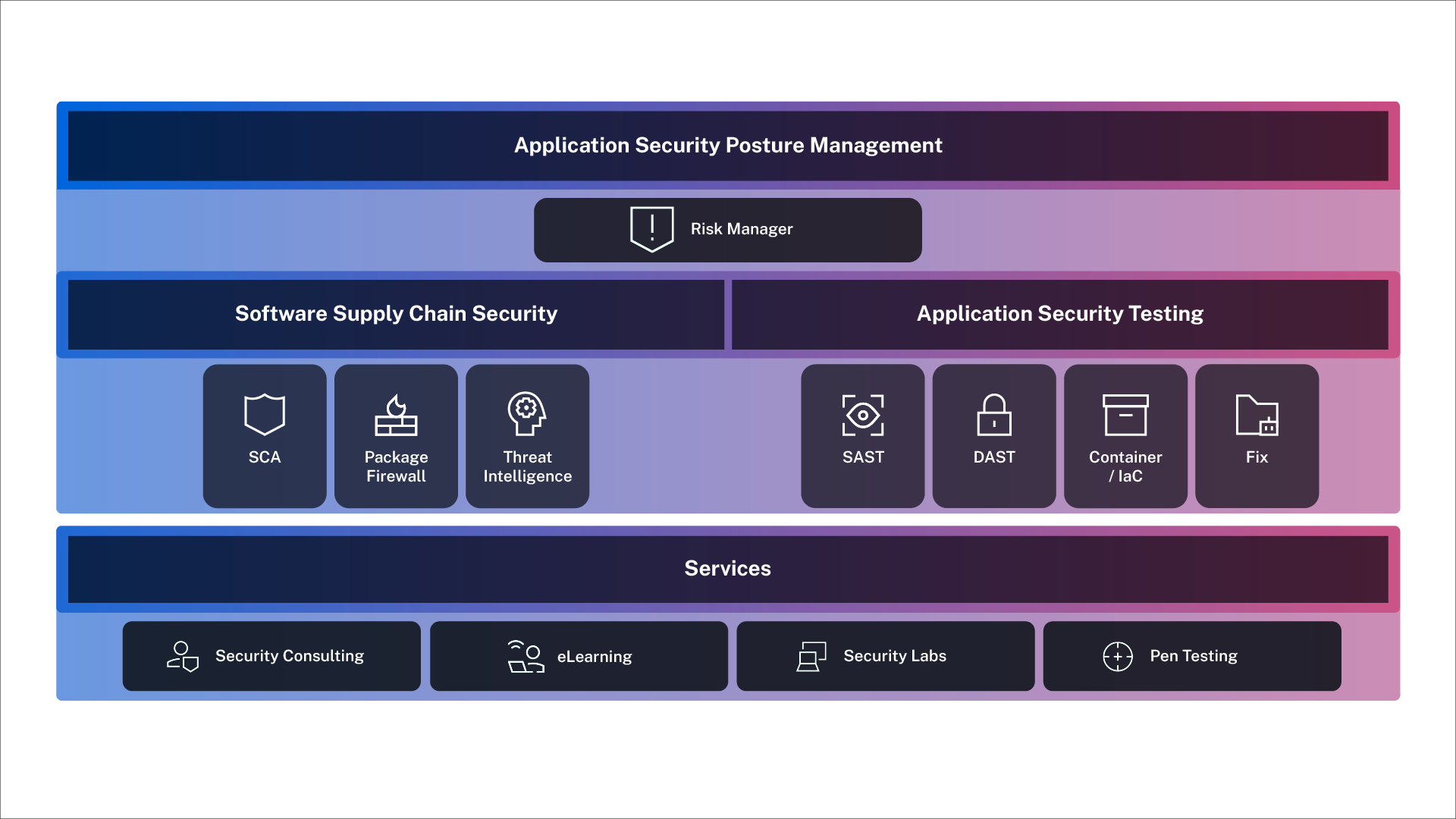
Comprehensive Application Risk Management
Veracode’s advanced AI-powered engine scans code in hundreds of languages to identify and resolve vulnerabilities at their core. Move beyond simple detection with root cause analysis that helps you prioritize and neutralize threats, minimizing risk and empowering your team to build securely from the start.
Solutions that Deliver Across Your Organization

For C-Level Execs
Gain comprehensive visibility into your entire application risk across your organization, ensuring strategic alignment and informed decision-making for long-term business resilience.

For Security Teams
Enforce security policies with unparalleled accuracy. Proactively identify and prioritize critical flaws, reduce false positives, and streamline remediation, enhancing your security posture and freeing up resources.

For Developers
Ship fully secure code faster. Get precise, developer-centric guidance within your workflow. Whether you’re using AI, third-party libraries, or vibe coding, catch vulnerabilities earlier, and deliver high-quality, trusted applications with confidence.