The software supply chain continues to face escalating threats, with malicious actors targeting developers and organizations at an unprecedented scale. In our Spring 2026 Threat Research Review, we analyze the latest trends, uncover alarming statistics, and highlight the evolving tactics used by attackers. From dependency injection attacks to the rise of typosquatting, this report provides a comprehensive look at the threats shaping the software ecosystem.
Discover how the NPM ecosystem remains a hotbed for malicious activity, the impact of new AI-driven tools like OpenClaw, and the critical steps your organization can take to stay ahead of these growing risks.
Key Findings
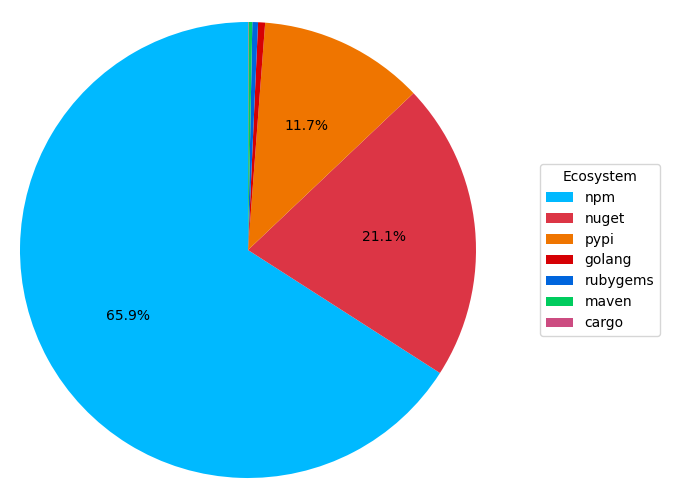
It shouldn’t be a surprise that the NPM ecosystem continues to be the most active with 65.9% of the packages we see. This is a trend we have been seeing for some years now and whilst we are seeing increased package volume in all ecosystems, NPM is growing the fastest.
Here are some stats on the malicious behaviours we identified this past quarter:
- 110 packages were specifically designed to target groups or organizations, often linked to cyber espionage or financial theft.
- 42,313 packages contained URLs known to be malicious, underscoring the growing risk of dependency injection attacks.
- 89,373 packages executed suspicious code during installation.
- 13,925 packages made server requests to IP addresses, attempting to communicate with command-and-control servers.
- 555,258 packages attempted to obfuscate their underlying code, making detecting malicious activity much more difficult.
- 4,708 packages were identified as typosquats, indicating a concerted effort by attackers to trick developers into installing malicious versions of popular packages.
- 33,675 packages were flagged as containing critical malware, requiring immediate attention.
Trends
We observed a sharp and continued increase across nearly all categories of malicious behavior except Dependency Confusion. The data reveals a clear shift in attacker methodology: threat actors are abandoning older, easily detectable methods in favor of highly deceptive, direct-compromise tactics.
(Note: In the data chart below, the Spring 2026 reporting period is represented as Q4 to align with our annual research tracking calendar.)
| Malicious Behaviour | Q3 | Q4 | Change |
| Dependency confusion | 481 | 110 | ⬇️ 77.1% |
| Malicious URLs | 15,153 | 42,313 | ⬆️ 179.2% |
| Suspicious install code | 60,630 | 89,373 | ⬆️ 47.4% |
| Malicious IP addresses | 9,563 | 13,925 | ⬆️ 45.6% |
| Obfuscation | 336,410 | 555,258 | ⬆️ 65.1% |
| Typosquats | 2,305 | 4,708 | ⬆️ 104.3% |
The Decline of Dependency Confusion
Relying on dependency confusion is becoming less favorable among attackers, dropping by a massive 77.1%. As organizations adopt stricter package scoping and private registry controls, this once-popular vector is yielding lower success rates. Attackers are pivoting toward tactics that exploit human error rather than system misconfigurations.
The Surge in Malicious URLs and Typosquatting
The most alarming spikes occurred in Malicious URLs (up 179.2%) and Typosquatting (up 104.3%). Attackers are actively banking on developers making slight typographical errors when pulling down popular packages. Once a typosquatted package is installed, it frequently calls out to a malicious URL to download a secondary payload. This dramatic rise indicates a highly coordinated effort to inject malicious dependencies directly into developer environments.
Escalating Obfuscation and Suspicious Execution
Code obfuscation grew by 65.1%, reaching over half a million packages. Threat actors are investing significant effort into hiding their malware, utilizing complex packing and encryption to evade automated security scanners. Paired with a 47.4% increase in suspicious install code and a 45.6% jump in malicious IP communications, the data points to more sophisticated, multi-stage attacks. Malware is no longer just sitting dormant; it is actively executing scripts during the build process and establishing connections with external command-and-control servers before the code ever reaches production.
Rise of Claw
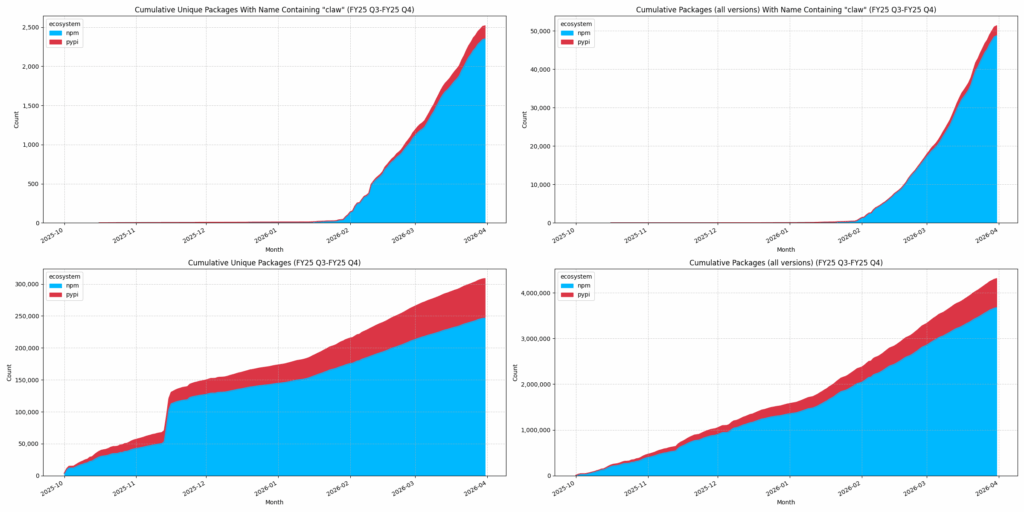
The end January marked the beginning of a new era of personal AI assistants; namely OpenClaw. With that we noticed an immediate and exponential volume of packages featuring the word “claw” in their name in the NPM ecosystem, and to a lesser extent within the PyPI ecosystem. Whilst claw has it’s own skills marketplace (ClawHub), it is interesting to see these types of packages to be distributed in the NPM ecosystem.
What makes it challenging for malware hunters is that these packages typically contain many files and they exhibit malware behaviours due to the nature of this tool, as we previously blogged about.
The graphs below should demonstrate this. on the left we are looking at unique packages and on the bottom we are looking at all package versions. On the top we have those packages with “claw” in the name. The exponential growth can be seen in the top charts, whereas how that impacts the whole volume is seen in the bottom charts.
Noteworthy Campaigns
As we previously reported, the Axios NPM account compromise was a big deal. Due to the volume of packages that depend on this extremely popular library there was a lot of fall out and many packages were affected.
Staying Safe
Supply chain risks are increasing in scale and complexity. Attackers now target not only servers, but also browsers and end users, through high-trust dependencies. Standard reactive security is no longer sufficient.
Veracode empowers you to adopt a proactive, defense-ready stance, protecting your developers, your users, and your business from the next wave of sophisticated supply chain attacks.
Discover how to reduce risk across your software supply chain without slowing down developer productivity in our upcoming webinar, or reach out to learn more.


