For today’s DevSecOps teams, the demands continue to intensify. Application portfolios and codebases continue to grow, while cyberattacks remain an ever-present danger. More than ever, it’s vital to ensure security gaps are identified and addressed with maximum speed and efficiency. In order to do this, you need to establish a continuous feedback loop on security threats, so you can realize optimized, sustained results – which is exactly how Veracode helps. Here we’ll outline how you can get started with Veracode in a matter of minutes, and we’ll detail all the ways we can help after your initial scans are complete.
How to Quickly Get Started with Veracode
Here’s an overview of the process of getting started with Veracode in two environments: GitHub and Azure. For each, we’ll outline the process for doing scans using our Veracode Static Analysis (SAST) and Veracode Software Composition Analysis (SCA) solutions. These solutions offer the fastest way to get scanning coverage in your continuous integration/continuous delivery (CI/CD) pipeline.
With these solutions, teams can write a few lines of YAML code and very quickly get results across the entire application portfolio, whether you’re running dozens or hundreds of applications. In this way, you can gain a complete understanding of the security posture of your applications.
GitHub Example:
Within GitHub, you use a GitHub action to get started. Type in “Veracode” to access, and you’ll see there is an “upload and scan” option. To create a GitHub workflow, you can either leverage existing YAML code or write new code.
Then you’re ready to build or artifact the code and submit it for static and SCA analysis. To do so, just submit the application name and enter your Veracode API key and ID.
When the GitHub workflow runs, the application will be built and submitted for a scan. The scans will run and generate results. You’ll get a complete look at code, including both first- and third-party code. Moving forward, you can put this functionality into existing CI/CD workflows, so scans run directly after a new artifact has been created.
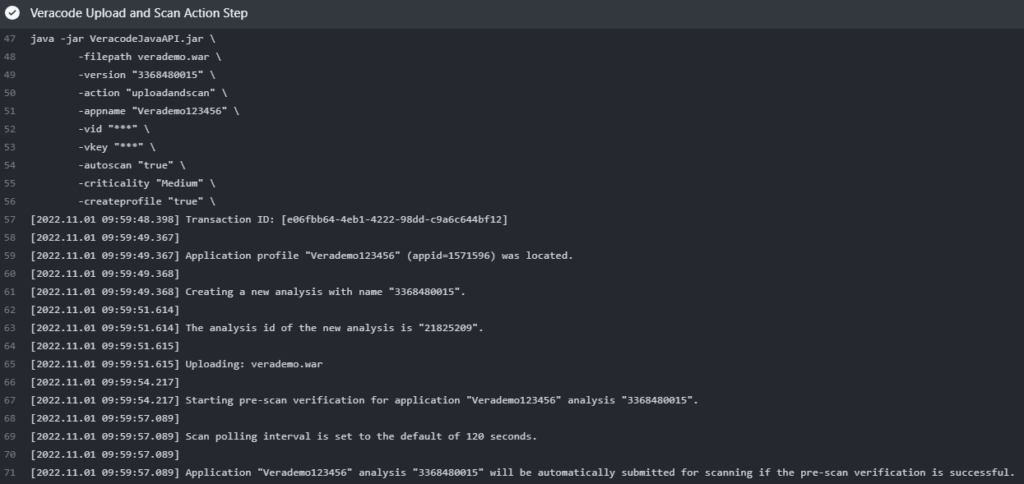
Azure Example:
To get started in Azure, you can leverage our plugin from the marketplace to submit your build artifact for scanning. Enter your Veracode API ID and key as variables and add Veracode as a step in your build pipeline.
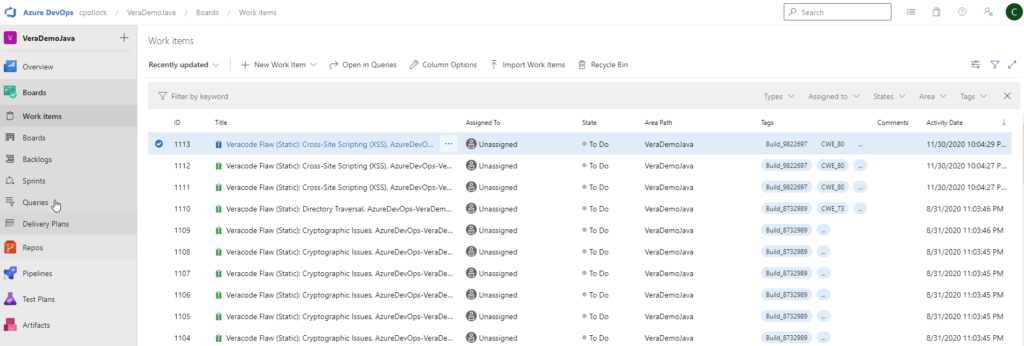
Next, select the submit command for a static and SCA scan, and you will get results right away. When the scan is complete, results will be published, typically as an artifact within the build job. You can view the results in the Veracode platform, in your IDE, in Azure Work Items, or any ticketing system of your choice.
Leveraging Scan Results and Next Steps
Once you’ve run your initial scans, Veracode solutions and services can assist with a range of efforts:
- Analysis. After generating results, Veracode offers the dashboards, reporting, and contextual guidance that help your DevSecOps teams assess vulnerabilities, determine which will need to be fixed and in what priority, and which can be mitigated.
- Ongoing, automated scanning. Once initial scans are done, you can set up subsequent scans to run routinely, for example after each new code commit. As a result, your teams will be notified of new flaws as soon as they’re introduced.
- Expanded scanning. As needed, you can efficiently augment your static and SCA scanning to incorporate dynamic and container scanning. For your highly critical applications, you can also employ manual penetration testing.
- Governance. Veracode solutions offer a range of governance capabilities. With these solutions, you can demonstrate the steps taken to address issues, whether open-source code libraries are current, and so on. The solution can create a software bill of materials (SBOM) that can be managed alongside other application artifacts. These results can be furnished to auditors, business leaders, partners, and customers.
- Targeted learning. By gaining an effective understanding of the security posture of your entire application portfolio, you can make more informed decisions in instituting ongoing enhancements. For example, you can identify problem areas within specific teams, and pursue coaching and training efforts to address skills or knowledge gaps. Further, you can identify strategies for moving testing earlier in the lifecycle to boost both efficiency and security.
Conclusion
To mitigate the threat of devastating cyberattacks, it’s critical that your teams scan your entire app portfolio for vulnerabilities, and to continue to scan as your codebase evolves. The good news is that Veracode enables you to quickly do initial scans, and to seamlessly integrate this scanning into your ongoing workflows. With Veracode solutions for static, dynamic, and SCA scanning, your teams can gain the insights to fuel effective remediation and mitigation of threats. Your teams can ensure code bases are stable and secure and leverage continued, automated scanning to identify any new threats that may arise.
For more than 17 years, we’ve been helping teams achieve their security objectives while maximizing their speed and efficiency. With our SaaS-based application security solutions, your teams can leverage patented technology that can model your application’s first- and third-party code in a unified fashion. This holistic visibility is critical because attackers are simply going after any weaknesses they can find; they don’t care whether those gaps are in first- or third-party code.
With our solutions, you can establish a continuous feedback loop on security threats, so you can realize optimized, sustained results. Our solutions enable your teams to leverage ongoing scanning and intelligent automation to secure existing applications, and then seamlessly address new flaws as they arise. Schedule a demo today.

