Years of accumulated security debt due to unaddressed software vulnerabilities and inadequate security configurations plague the applications that support our government functions. The age and size of applications play a significant role in the accumulation of security debt. The State of Software Security 2024 report provides a detailed analysis of how these factors correlate with security vulnerabilities, particularly in older and larger applications. Here are some key insights from our report focusing on the public sector.
The Growing Burden of Aged Applications
For the purposes of the report, we define security debt as flaws that remain unremediated for over one year. Our findings indicate that security debt is not uniformly distributed across all applications. Naturally, it tends to concentrate in applications that are older and have grown larger over time.
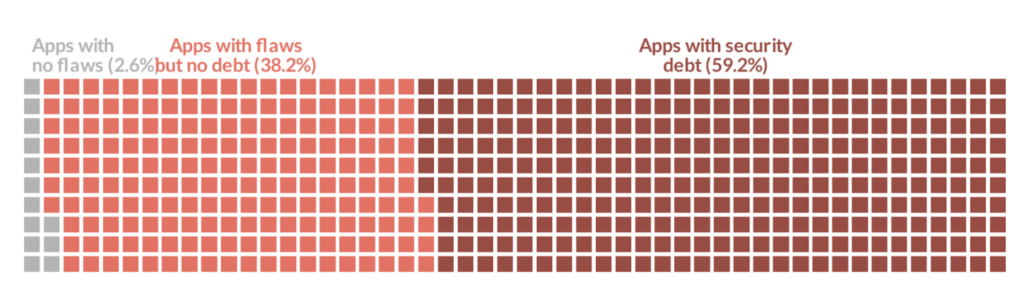
This trend is particularly pronounced in the public sector, where 59% of applications carry some form of security debt, which is higher (worse) than the overall rate of 42%. Furthermore, just 2.6% of applications are flaw-free, compared to 5.9% across other industries.
Security debt in the public sector tends to concentrate in older, larger applications. This is especially true for critical security debt, defined as the portion of security debt comprised of high-severity flaws. 30.4% of public sector applications carry critical security debt, which typically poses the highest risk.
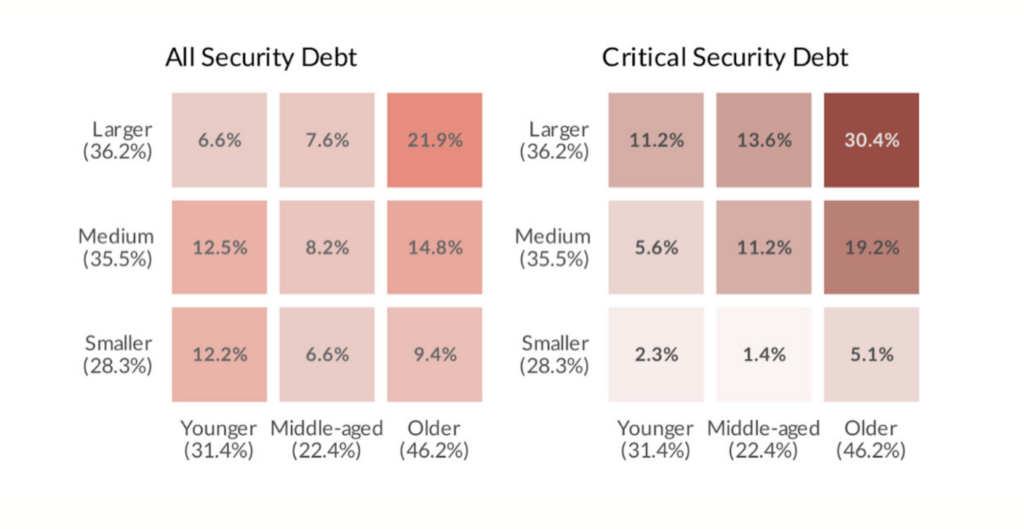
Applications are considered younger if they’re between 1 and 2.1 years old, middle between 2.1 and 3.4 years), and older after 3.4 years. Those are admittedly weird breakpoints, but they roughly divide all applications into three equal bins. We took a similar approach for grouping small (<250kB), medium (250kB-1.55MB), and large (1.55MB+) applications based on the size of their codebase.
Why Older and Larger Applications Get More Vulnerable
As applications age, they typically undergo numerous updates, feature additions, and integrations. Each iteration can introduce new vulnerabilities, particularly if not all updates are continuously vetted for security flaws. The State of Software Security 2023 report revealed that in any given month there’s a 27% chance that flaws will be introduced into an application. Larger applications, due to their complexity and the sheer volume of code, are more challenging to manage and secure. They provide more opportunities for security lapses and make comprehensive code reviews more cumbersome.
Additionally, third-party components accumulate risk over time as new vulnerabilities are discovered. So, even if developers are not adding new code, an application will become more vulnerable unless all dependencies are kept up to date.
Implications for Public Sector Security
The concentration of security debt in older, larger applications has significant implications for public sector organizations. Many of these entities rely on legacy systems that are integral to their operations, making them susceptible to security breaches if these systems are not adequately maintained.
Our Advice: Strategic Remediation Efforts Responsibly Leveraging AI
To address this issue, public sector organizations need to prioritize their remediation efforts. The analysis suggests focusing on older, larger applications and directing resources towards identifying and fixing high-severity flaws in critical debt first. By tackling the most critical vulnerabilities, organizations can significantly reduce their overall risk exposure.
Veracode’s AI-driven remediation tool, Veracode Fix, can address many Common Weakness Enumeration (CWE) categories with severity ratings ranging from medium to very high. This innovative approach, leveraging a curated set of reference patches from our security research team, enables organizations to proactively reduce security debt and strengthen their software security posture.
Conclusion
The correlation between the age and size of applications and the accumulation of security debt in the public sector underscores the need for a strategic approach to software maintenance. Prioritizing older and larger applications for targeted remediation efforts built into sprints can help mitigate the risks associated with this security debt, ensuring that public sector entities can continue to serve their constituents securely and efficiently. This targeted approach not only enhances security but also optimizes resource allocation, making it a critical strategy for public sector development organizations moving forward.
Download the full public sector snapshot for more information.


