You can’t fix what you ignore. For years, organizations have raced to deploy software faster, often leaving a trail of unresolved vulnerabilities in their wake. We call this trail security debt, or flaws that are left unresolved over a year since being discovered, and it isn’t just a technical metric. It’s a compounding business risk that is growing harder to manage every year.
Today, we are releasing the 2026 State of Software Security (SoSS) report. The data is clear: the volume of risky code lingering in codebases is expanding, and high-severity flaws are becoming more common. But this year’s report offers more than just a warning. It provides a structured, data-backed strategy to regain control.
If you feel like you are drowning in vulnerabilities, you aren’t alone. But you also don’t have to stay there.
The Chaos: Rising Debt and High Risk
The numbers from this year’s analysis paint a stark picture of the modern development landscape. Security debt is not some edge case; it’s the norm, and it’s growing fast.
According to our 2026 findings:
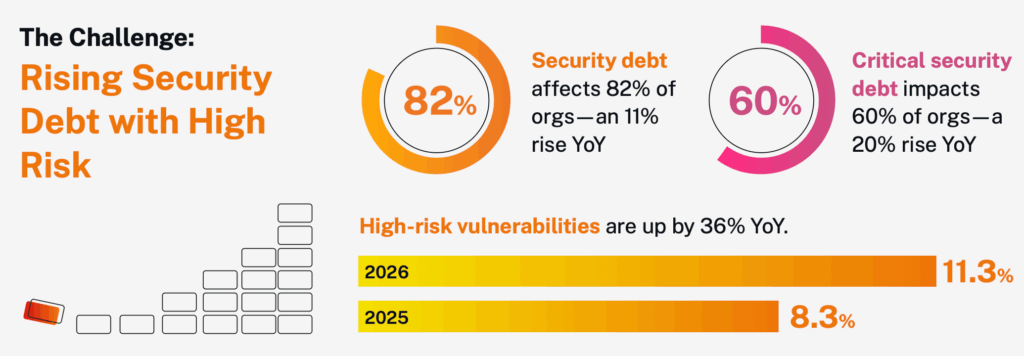
- Security debt now affects 82% of organizations. That represents an 11% increase year-over-year (YoY).
- Critical security debt impacts 60% of organizations. This is a 20% relative increase from 2025.
- High-risk vulnerabilities are up by 36% YoY.
These statistics reveal a fundamental tension in software development. Teams are pushing code to production at record speeds, often fueled by AI-generated code and automated pipelines. However, the mechanism for fixing flaws hasn’t kept pace with the mechanism for creating them.
Here’s the thing: security debt is growing faster. In 2024, security debt affected 71% of orgs and critical debt affected 46% of orgs. In 2025, security debt affected 74% of orgs and critical debt affected 50% of orgs. Now in 2026, it’s 82% and 60% of orgs affected by security debt and critical debt, respectively.
When 60% of organizations are carrying critical security debt, it means the majority of businesses are operating with known, severe vulnerabilities that leave the door open to attackers. This isn’t just “tech debt” that slows down features; it is “risk debt” that threatens the bottom line.
Finding Clarity in the Chaos
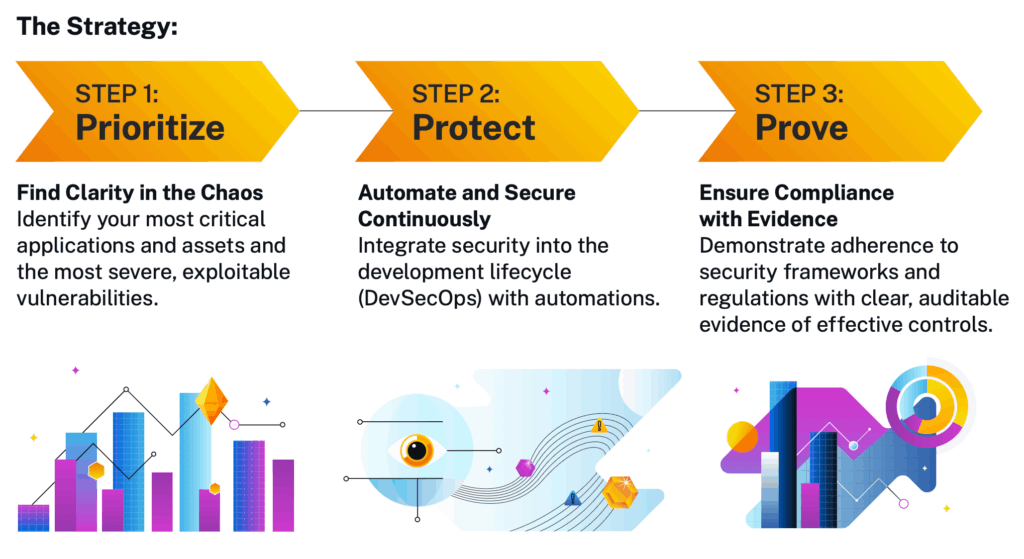
The sheer volume of vulnerabilities can be paralyzing. When everything is flagged as “urgent,” nothing gets fixed. The 2026 SoSS report outlines a three-step framework to cut through the noise and reduce risk effectively: Prioritize, Protect, and Prove.
Step 1: Prioritize
You cannot fix everything at once. Attempting to do so is a guaranteed recipe for burnout and failure. The most successful organizations move away from “fix all flaws” to “fix the right flaws.”
This starts with visibility. You need to identify your most critical applications and assets. Not all apps are created equal; a public-facing payment portal carries significantly more risk than an internal cafeteria menu.
Once you know where your assets are, focus on the most severe, exploitable vulnerabilities. The data shows that high-risk vulnerabilities have risen by nearly 40%. These are the flaws that attackers are most likely to weaponize. By prioritizing these specific issues, you reduce your actual risk profile faster than if you tried to tackle the entire backlog of low-severity debt.
Step 2: Protect
Prioritization tells you what to fix. Protection ensures you can keep fixing it… continuously.
The 2026 data reinforces that manual security testing is obsolete. It acts as a bottleneck that developers will inevitably bypass to meet deadlines. To protect your software estate, you must integrate security directly into the development lifecycle (DevSecOps) using automation.
This means:
- Scanning early and often: Catching flaws while code is being written, not days after deployment. Utilize Static Analysis (SAST) for first-party code and Software Composition Analysis (SCA) for third-party code.
- Automating remediation: Using tools that suggest fixes or automatically apply patches where possible.
- Blocking builds: Establishing quality gates that stop critical vulnerabilities from ever reaching production.
When security is automated, it stops being a hurdle and starts being a guardrail. It allows developers to move fast without breaking things.
Step 3: Prove
Doing the work is half the battle. Proving you did it is the other half.
In 2026, regulatory pressure and board-level scrutiny are higher than ever. It is no longer enough to say you are secure; you must demonstrate adherence to security frameworks and regulations.
“Prove” means generating clear, auditable evidence of effective controls. This isn’t just about passing an audit. It’s about having the data to show stakeholders, from customers to the C-suite to auditors, that your security program is reducing risk over time. It transforms security from a “black box” into a measurable business function.
The Path Forward
The rise in security debt is a serious signal, but it doesn’t have to be a permanent state. The 11% rise in organizations affected by debt proves that the old ways of managing application security (scanning late, fixing later) are failing.
Your strategy for 2026 must be proactive. It requires shifting from reactive firefighting to a disciplined approach of prioritizing risk, protecting the pipeline, and proving compliance.
The tools and data exist to turn this trend around. By focusing on the vulnerabilities that matter most and automating the defenses that keep them at bay, you can stop managing debt and start managing security.


