Mark Twain famously said, "truth is stranger than fiction." I doubt even he could invent the strange events that unfold daily in our newsfeeds. In the realm of cybersecurity, however, breaches and vulnerabilities are becoming so frequent as to be predictable.
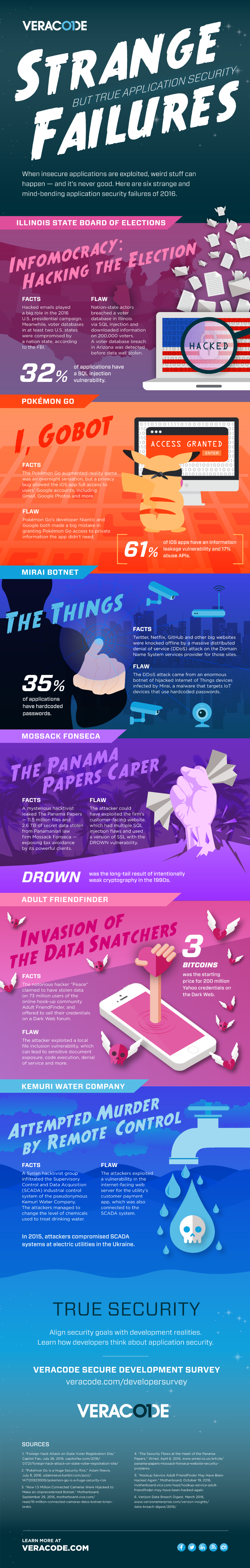
Nevertheless, some of the most notable breaches of the past year were shocking in their details. Look at the unexpected outcome of the U.S. presidential election, and the alleged cyberattacks by Russia. Beyond hacked emails and "fake news," at least two states had their voter databases breached, most likely through a SQL injection vulnerability, a disturbingly common web application security failure.
Many of the most bizarre breaches can be attributed to application-layer attacks, including last year's hack of the online hookup community Adult FriendFinder, with millions of users' credentials ending up for sale on the Dark Web. Stranger still, application security vulnerabilities allowed attackers to compromise the SCADA systems of a water utility through a public payment application. The attackers were able to mess with the control system to change the level of chemicals in the water, although the breach was caught in time to prevent potentially devastating consequences, according to the Verizon Data Breach Digest.
Then there was the story of the Mirai botnet, a collection of compromised Internet of Things devices used in a super-powerful DDoS attack that temporarily knocked several major websites offline. Mirai's masters built such a powerful botnet by exploiting hardcoded passwords in 1.5 million webcams.
These and other strange but true application security failures that caught our eye in the past year are the subject of this infographic. If you think of other strange AppSec failures that we missed, use the comments section to add to this list. And learn more about the application security challenges and frustrations developers struggle with in our developer survey report.