Note: Veracode acquired Phylum in January 2025, after this blog was published, and it has been migrated to Veracode’s blog.
Phylum can now be deployed directly with artifact repositories and package managers to vet open-source software packages before they enter an organization or developer workstations.
“Think of Phylum like a firewall for open-source software packages, providing a layer of defense between the open-source ecosystem and the software your customers trust you to keep secure,” said Aaron Bray, co-founder and CEO of Phylum.
Phylum users benefit from its powerful, automated analysis engine that reports proprietary findings instead of relying on manually curated lists. Phylum uses SAST, heuristics, machine learning, and artificial intelligence to detect and report zero-day findings. Users know more risks sooner and earlier in the development lifecycle for the strongest software supply chain defense.
“Because Phylum’s analysis engine looks at third-party code as soon as it’s published into the open-source ecosystem, we are uniquely positioned to inform organizations of the most threats, at pace, and at scale,” said Louis Lang, co-founder, and CTO at Phylum. “For example, public lists like OSV, which does its best to crowdsource the identification of malicious open-source packages, has reported a little over 25,000 malicious packages while Phylum has found more than 200,000.”
Phylum users benefit from its powerful, automated analysis engine that reports proprietary findings instead of relying on manually curated lists. Phylum uses SAST, heuristics, machine learning, and artificial intelligence to detect and report zero-day findings. Users know more risks sooner and earlier in the development lifecycle for the strongest software supply chain defense.
“Because Phylum’s analysis engine looks at third-party code as soon as it’s published into the open-source ecosystem, we are uniquely positioned to inform organizations of the most threats, at pace, and at scale,” said Louis Lang, co-founder, and CTO at Phylum. “For example, public lists like OSV, which does its best to crowdsource the identification of malicious open-source packages, has reported a little over 25,000 malicious packages while Phylum has found more than 200,000.”
“One customer, for example, wanted to ensure all packages they consumed were at least two weeks old. This use case was quickly satisfied by a custom policy, which took minutes to write and was deployed within three clicks to provide enterprise-wide enforcement. This option is now available in the Phylum Policy Library for any customer to use,” said Bray.
Given that for most organizations developer experience is of paramount importance, Phylum operates as seamlessly as possible. In the event a specific version of a package is non-compliant (e.g., contains a critical security vulnerability), Phylum can gracefully fallback to a compliant version of the requested package. The development process remains uninterrupted, secure software is used and a breakage is only caused if no viable alternatives exist.
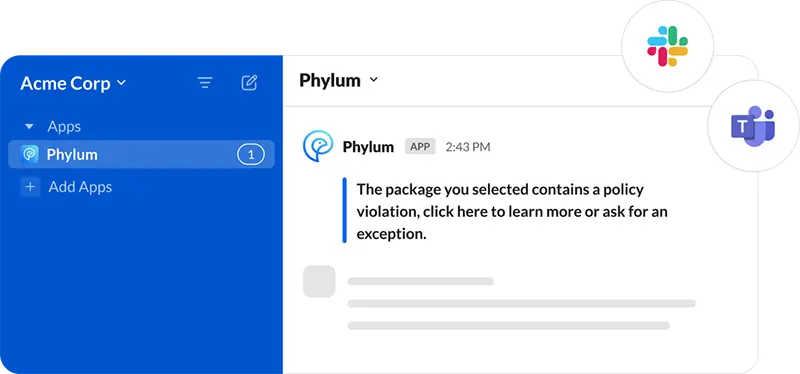
In addition, to avoid confusion, Phylum can integrate with enterprise communication tools like Slack or Teams to notify developers of issues that cannot be automatically remedied. It also provides a workflow in-line with the notification to request an exception to a policy, when needed. The net result of this set of capabilities is protection from threats and license issues, and less vulnerabilities in delivered software overall. This results in less friction between security and engineering organizations, less time spent correcting problems for software developers, and less time spent triaging findings for security teams.
Phylum also provides continuous monitoring, so users are notified when new issues arise, or a package exhibits risky behavior after use. Users can look up historical packages at any time, even after they have been removed from the open-source ecosystem, for incident response, governance, or policy adherence purposes. Phylum can also be deployed in the CI/CD pipeline.