Your Customers Want Secure Software
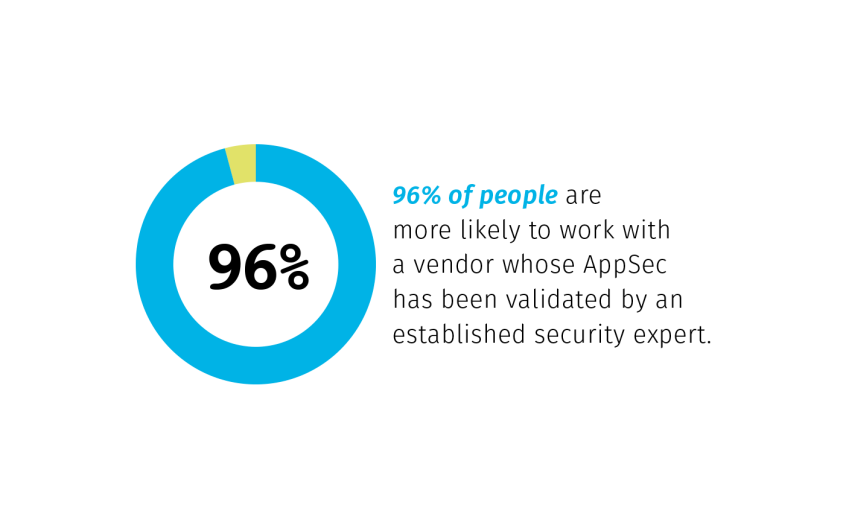
Customers, now more than ever, are security conscious. Application security practitioners everywhere recommend a variety of testing types that provide both depth and breadth of coverage, and time-to-remediation requirements to ensure applications are secured quickly. Veracode has designed the Veracode Verified program to secure development processes and improve your application security posture, and by participating, you show dedication to proven AppSec principles to your customers.

Secure Software Is a Competitive Advantage
Prove your company’s secure software development practices with Veracode Verified.
By participating in the Veracode Verified program, you’re empowered to make security part of your competitive advantage, easily defend your AppSec budget, and better integrate security with development by progressing through the Verified Tiers. You prove at a glance that you’ve made security a priority, and that your security program is backed by one of the most trusted names in the industry. And, sales teams and product marketing managers will have a powerful new way to win business.
Veracode Verified Program Tiers

Standard
• First-party code scanned
• Policy defined
• AppSec program implemented

Team
Standard Tier plus:
• Development security champion
• Open source library scanning

Continuous
Team Tier plus:
• Secure coding education
• Early SDLC integrations
With Veracode...

Quickly and Effectively Reduce Your Risk
-
AppSec must follow the speed of development, and Veracode Verified provides a proven model for your organization to adopt to continuously reduce risk.
-
The Veracode Verified program helps you achieve faster remediation times, integrate security directly into the development lifecycle, and train developers on secure coding.
-
Scale your program, stay ahead of customer and prospect security concerns, speed up your secure development, and provide value back to the business without straining limited security resources.

Demonstrate Your AppSec Program Value
-
Veracode Verified allows you to champion AppSec internally. Secure and defend your budget, investment, and program priority by measuring progress to your executive board.
-
Veracode Verified gives you a holistic, objective view of your AppSec program success. With a third-party assessment, you can evaluate and track the maturity of your program, and chart a path forward to take your most critical applications to higher tiers over time.
-
And, of course, demonstrate the success of your AppSec program to your customers and prospects.

Achieve Tighter Integration With Development
-
Empower your development teams to incorporate security into their everyday workflows.
-
Cultivate security champions to drive DevSecOps practices, arm them with training and resources to be successful, and leverage them as a connection between security and development teams.