DevSecOps Program Management
A platform that unifies development and security delivers a successful secure DevOps program.

Why the Veracode Platform Can Help You Deliver a Successful DevSecOps Program?
Platform Capabilities
Continuous Scanning
Reduce risks at every phase of development with Veracode Static Analysis, Dynamic Analysis, Software Composition Analysis, Manual Penetration Test, and more throughout your SDLC.
Meet Data Residency Requirements
Meet your data residency needs with our European instance on AWS based in Frankfurt, Germany, and your government security standards with a new FedRamp authorization from the United States Federal Government.
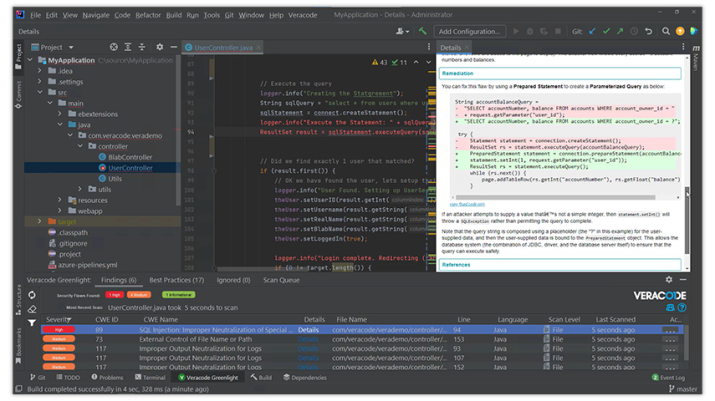
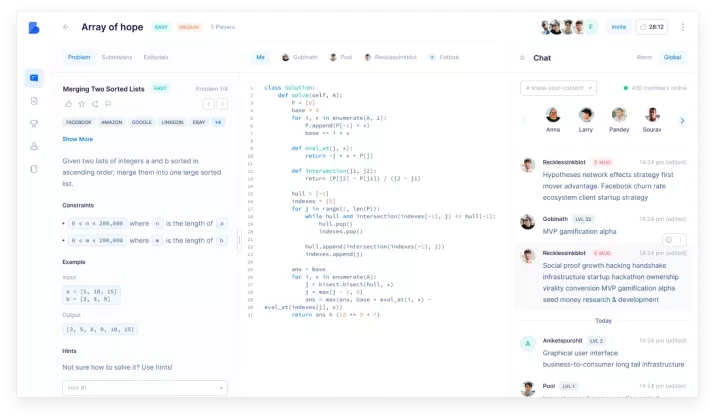
Frictionless Development
Quickly find and fix flaws at scale where your developers work with security integrated into the dev environment, automated remediation guidance, in-context learning like Security Labs, in an open and extensible platform.
Contextual Platform Data
Predict future vulnerabilities with self-healing capabilities over the time, through applying machine learning and artificial intelligence to data gained from nearly 2 decades of scanning and customer learning.
Comprehensive DevSecOps
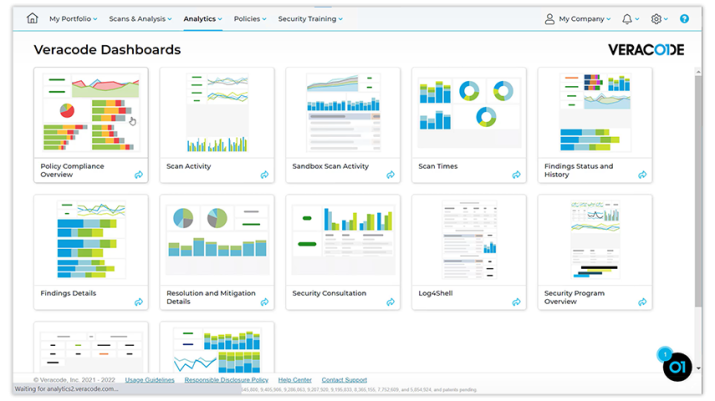
Streamline your governance, risk and compliance process with flexible policy management, unified reporting and analytics, and peer benchmarking to mitigate risks fast and deliver a successful DevSecOps program.
Cloud-Native SaaS Architecture
Provide elastic scalability, high performance, and lower costs with cloud-native SaaS architecture. You can focus on your DevSecOps program, not your infrastructure.
Continuous Scanning:
Comprehensive Approach:
Beyond Just Finding Flaws:
Veracode is Trusted by 2,600 Companies Globally
Featured Resources